Director of Software Engineering
Chris Armour
The Breaker & Builder.
Operating on the philosophy that 'you can't build a secure system if you don't know how to break it,' Chris leads our engineering division. A top 1% National Cyber League competitor, he hardens our digital infrastructure against the very exploits he has mastered.
Access Dossier// Operational Intelligence Feed
168 Dispatches Found
Cybersecurity
Apr 11, 2026
External Attack Surface Management: Why Attackers Know Your Infrastructure Better Than You Do
Access File Security News
Apr 11, 2026
CPUID Supply Chain Attack Distributes STX RAT, Three Gangs Drive 40% of March Ransomware
Access File Compliance News
Apr 11, 2026
63 Healthcare Breaches in February Expose 8.1 Million Records, OCR Releases HIPAA Guidance
Access File Privacy News
Apr 11, 2026
EFF Fights Section 702 Clean Extension, Post-Quantum Crypto Deadline Moved to 2029
Access File Cyber Security, Tech Innovations in Security
Jan 4, 2026
Client-Side Supply Chain Defense: Mastering Content Security Policy (CSP) for Modern Apps
Access File Cyber Security, Privacy News, Security Insights, Security News
Jan 3, 2026
California DROP Tool: A New Era of Data Accountability
Access File Cyber Security, Tech Innovations in Security
Dec 28, 2025
API Security Guardrails: Implementing Fine-Grained Authorization to Neutralize BOLA Risks in 2026
Access File Artificial Intelligence, Cyber Security, Tech Innovations in Security
Dec 2, 2025
Secure Coding for AI: Preventing Data Poisoning and Model Evasion in Your ML Applications
Access File Security News
Dec 1, 2025
Android Zero-Days, NPM Malware, CISA Alerts & ICS Flaws – 12/02/2025
Access File Security News
Nov 27, 2025
Supply Chain Attacks, Tomiris APT & CISA KEV Alert – 11/28/2025
Access File Privacy News
Nov 26, 2025
OpenAI Breach, Student Privacy & EU Social Media Ban – 11/27/2025
Access File Compliance News
Nov 26, 2025
SFO Guidance, Anti-Smuggling, Greenwashing & FCA – 11/27/2025
Access File Cyber Security, Tech Innovations in Security
Nov 25, 2025
WebAssembly Security: Hardening the Next Generation of Cloud-Native and Edge Applications
Access File Compliance News
Nov 23, 2025
Oracle Vulnerability, Coinbase Fine & Bribery Act – 11/24/2025
Access File Cyber Security, Security Insights
Nov 21, 2025
Living Off the Land Attacks: A Practitioner's Playbook for Detecting the Undetectable
Access File Security News
Nov 19, 2025
WhatsApp Leak, AI Laws, Phishing Scams & Patent Rules – 11/20/2025
Access File Compliance News
Nov 18, 2025
Fortinet Exploit, NIH Audit, Data Breach & EUDR – 11/19/2025
Access File Compliance News
Nov 16, 2025
Healthcare Breaches, CCPA, AI Risk & GC Trends – 11/17/2025
Access File Security News
Nov 15, 2025
Microsoft Zero-Day, Logitech Breach & Patch Tuesday – 11/16/2025
Access File Security News
Nov 14, 2025
XWiki Exploit, FortiWeb Attacks & Finger Malware – 11/15/2025
Access File Security News
Nov 13, 2025
AI Cyberattacks, Fortinet Zero-Day & Akira Ransomware – 11/14/2025
Access File Cyber Security, Security Insights
Nov 8, 2025
The Diamond Model of Intrusion Analysis: A Practitioner's Guide to Threat Intelligence
Access File Compliance News
Nov 7, 2025
Mobile Malware, AI Security, Regulatory Compliance – 11/08/2025
Access File Privacy News
Nov 7, 2025
Spyware, Car Surveillance, Firewall Flaws & Breaches – 11/08/2025
Access File Cyber Security, Tech Innovations in Security
Nov 5, 2025
API Fuzz Testing: A Practical Guide to Finding Security Flaws Before Attackers Do
Access File Compliance News
Nov 5, 2025
Zero-Day, ChatGPT Bugs, FINRA Fine & Data Breaches – 11/06/2025
Access File Security News
Nov 3, 2025
ICS Vulnerabilities, WordPress Exploit & Russian Malware – 11/04/2025
Access File Compliance News
Nov 3, 2025
OpenAI Backdoor, Healthcare Breach & Ransomware – 11/04/2025
Access File Privacy News
Nov 3, 2025
Racist Policing, Ring Privacy, App Censorship & Payroll Scams – 11/04/2025
Access File Cyber Security, Tech Innovations in Security
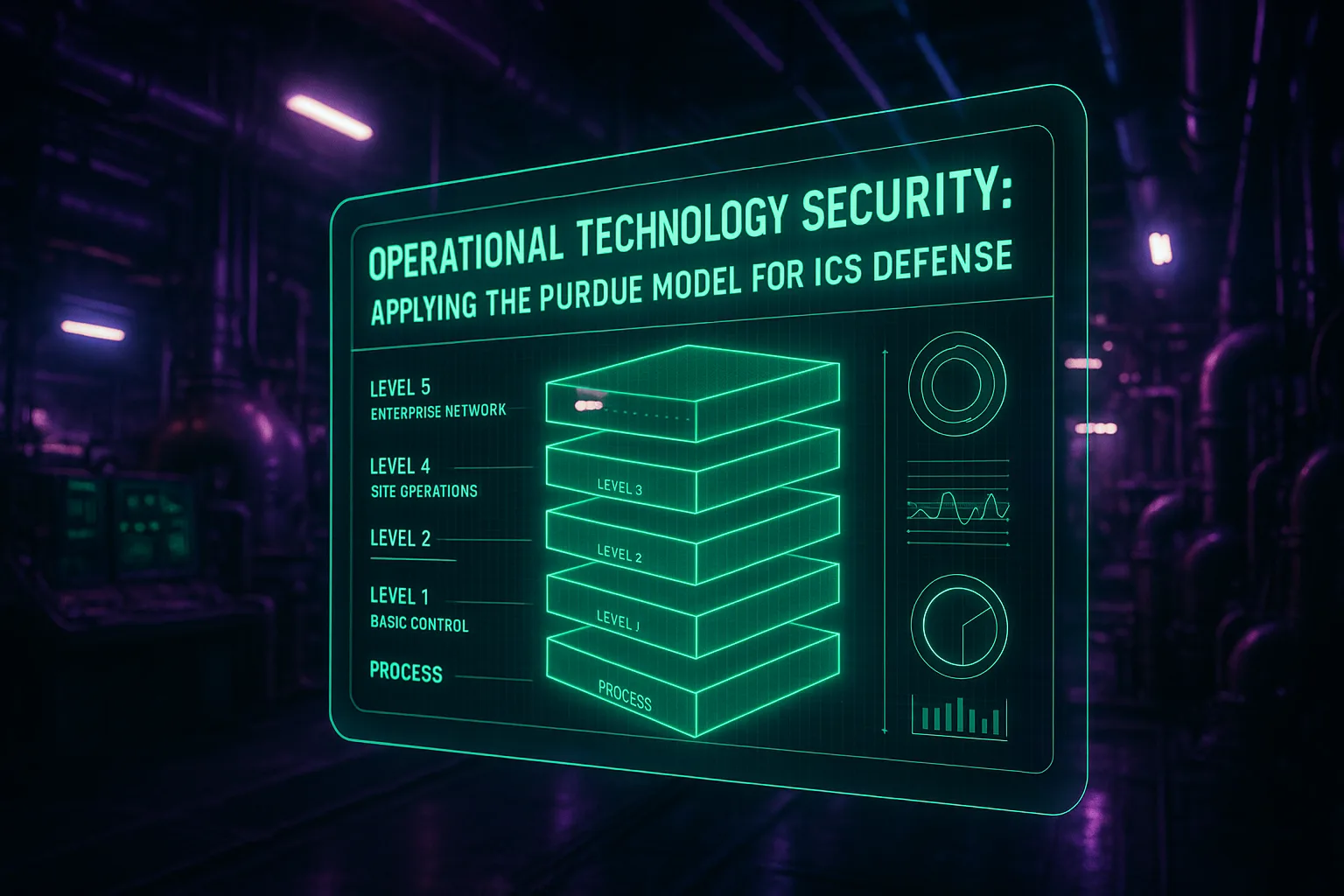
Nov 2, 2025
Operational Technology Security: Applying the Purdue Model for ICS Defense
Access File Security News
Oct 27, 2025
TEE.Fail Attack, Qilin Ransomware, CISA Alerts & BlueNoroff – 10/28/2025
Access File Compliance News
Oct 24, 2025
Windows Patch, Pay Transparency, AI Act & FCPA – 10/25/2025
Access File Security News
Oct 23, 2025
WSUS Vulnerability, WordPress Exploits & GlassWorm Worm – 10/24/2025
Access File Cyber Security, Tech Innovations in Security
Oct 16, 2025
Malicious Code Forensics: A Practitioner's Guide to Reverse Engineering Malware from Compromised IoT Devices
Access File Compliance News
Oct 16, 2025
Ransomware, Data Breach, NY DFS, & Password Risks – 10/17/2025
Access File Compliance News
Oct 15, 2025
Cyber Threats, Healthcare Breach, & AML Updates – 10/16/2025
Access File Privacy News
Oct 14, 2025
Apple Bounty, Android Attack, Surveillance & MANGO Breach – 10/15/2025
Access File Compliance News
Oct 14, 2025
Data Breach, CCPA, Oracle Attack & Patch Update – 10/15/2025
Access File Security News
Oct 13, 2025
Windows Zero-Days, Patch Tuesday & Android Attacks – 10/14/2025
Access File Cyber Security, Physical Security, Tech Innovations in Security
Oct 12, 2025
Smart Building Security: Protecting Your Facility's HVAC, Lighting, and Elevator Systems from Cyber-Physical Threats
Access File Privacy News
Oct 12, 2025
Student Data, AI Ethics, Data Breaches & Regulations – 10/13/2025
Access File Security News
Oct 10, 2025
SonicWall VPN Attacks, LockBit Tactics & Apple Bounties – 10/11/2025
Access File Privacy News
Oct 10, 2025
Zero-Day Exploit, Data Scraping & Foster Youth Risks – 10/11/2025
Access File Cyber Security, Tech Innovations in Security
Oct 8, 2025
Container Escape Vulnerabilities: A Technical Deep Dive for DevOps and Cloud Security Teams
Access File Security News
Oct 5, 2025
Oracle Zero-Day, Clop Attacks & GoAnywhere Exploit – 10/06/2025
Access File Cyber Security, Tech Innovations in Security
Oct 4, 2025
eBPF for Security: A Practitioner's Guide to Cloud-Native Threat Detection
Access File Security News
Oct 4, 2025
Zimbra Zero-Day, Gov Cloud Loss, & ParkMobile Breach – 10/05/2025
Access File Compliance News
Oct 3, 2025
Export Controls, AI Safety, Lapsus$ & Cybersecurity – 10/04/2025
Access File Security News
Oct 3, 2025
Palo Alto Scans, Discord Breach & AI CometJacking – 10/04/2025
Access File Cyber Security, Tech Innovations in Security
Oct 1, 2025
Memory-Safe Languages: How Rust is Eliminating Entire Classes of Security Vulnerabilities
Access File Cyber Security, Tech Innovations in Security
Sep 28, 2025
Confidential Computing Implementation: A Developer's Guide to Protecting Data-in-Use with Secure Enclaves
Access File Security News
Sep 28, 2025
CISA KEV, SonicWall Attacks, JLR Breach & AI Threats – 09/29/2025
Access File Security News
Sep 25, 2025
GoAnywhere Flaw, Cisco Exploits & LockBit Variant – 09/26/2025
Access File Cyber Security, Tech Innovations in Security
Sep 24, 2025
Securing OT-Cloud Integration: A Practical Playbook for Bridging the Air Gap Without Compromising the Plant Floor
Access File Security News
Sep 23, 2025
Cisco Zero-Day, BRICKSTORM Malware & Supermicro Flaws – 09/24/2025
Access File Security News
Sep 22, 2025
NPM Supply Chain, GeoServer Exploit & CISA Alerts – 09/23/2025
Access File Cyber Security, Tech Innovations in Security
Sep 21, 2025
Automated DevSecOps Governance: Integrating VEX and SBOMs into Your CI/CD Pipeline for Real-Time Risk Triage
Access File Security News
Sep 21, 2025
Airport Ransomware, Stellantis Breach & AI Risks – 09/22/2025
Access File Security News
Sep 20, 2025
Entra ID Flaw, Airport Cyberattack & AI Security – 09/21/2025
Access File Security News
Sep 18, 2025
GoAnywhere Flaw, Russian APTs & Scattered Spider – 09/19/2025
Access File Security News
Sep 17, 2025
Scattered Spider Arrest, Chrome Zero-Day & AI Threats – 09/18/2025
Access File Cyber Security, Tech Innovations in Security
Sep 16, 2025
GraphQL Security Blind Spots: A Developer's Playbook for Preventing Data Exposure and Resource Exhaustion Attacks
Access File Security News
Sep 16, 2025
Salesforce Breach, JLR Production Halt & SonicWall Alert – 09/17/2025
Access File Security News
Sep 14, 2025
FBI Salesforce Warning, Ransomware & Rowhammer Bypass – 09/15/2025
Access File Security News
Sep 13, 2025
Salesforce Threats, VoidProxy Phishing & AI Risks – 09/14/2025
Access File Artificial Intelligence, Cyber Security, Tech Innovations in Security
Sep 12, 2025
CNAPP Optimization with AI: A Technical Playbook for Automating Cloud Threat Response
Access File Security News
Sep 11, 2025
Exploited Vulns, HybridPetya Ransomware & Spyware – 09/12/2025
Access File Security News
Sep 10, 2025
SonicWall Exploits, VMScape Attack, Siemens Flaws, and Rising Spyware Risks
Access File Artificial Intelligence, Cyber Security, Tech Innovations in Security
Sep 9, 2025
Digital Twin Security: A 2025 Playbook for Protecting Critical Infrastructure
Access File Security News
Sep 9, 2025
Kerberoasting Attacks, Jaguar Land Rover Breach, and Malicious NPM Package
Access File Cyber Security, Tech Innovations in Security
Sep 8, 2025
Fine-Grained Authorization: A Technical Guide to Implementing Modern Access Control for Microservices
Access File Cyber Security, Tech Innovations in Security
Sep 4, 2025
VEX in DevSecOps: How to Use the Vulnerability Exploitability eXchange to Prioritize Real Threats
Access File Cyber Security, Tech Innovations in Security
Aug 29, 2025
Service Mesh Security: A Deep Dive into mTLS and Access Control for Microservices
Access File Artificial Intelligence, Cyber Security, Tech Innovations in Security
Aug 25, 2025
Automated Threat Hunting: Integrating SOAR and AI to Proactively Find Hidden Adversaries
Access File Artificial Intelligence, Cyber Security, Tech Innovations in Security
Aug 21, 2025
Securing LLM APIs: A Technical Playbook for Preventing Prompt Injection and Data Exfiltration
Access File Artificial Intelligence, Cyber Security, Tech Innovations in Security
Aug 18, 2025
CNAPP Implementation: A Practical Guide to Unifying Cloud Security from Code to Production
Access File Cyber Security, Security Insights
Aug 13, 2025
Zero Trust Architecture Implementation: A Phased Approach to Eliminating the Perimeter
Access File Cyber Security, Security Insights, Tech Innovations in Security
Aug 11, 2025
API Security Best Practices: Why Your APIs Are the New Shadow IT and How to Protect Them
Access File Cyber Security, Security Insights
Aug 9, 2025
Cyber Supply Chain Security: A 2025 C-Suite Guide to SBOMs and C-SCRM
Access File Cyber Security, Physical Security, Security Insights
Aug 8, 2025
Biometric Data Security: A 2025 Guide to Protecting Your Most Irreplaceable Assets
Access File Artificial Intelligence, Cyber Security, Security Insights
Aug 7, 2025
Beyond the Perimeter: Using AI to Detect Insider Threats Before They Strike
Access File Artificial Intelligence, Cyber Security, Security Insights
Aug 6, 2025
Deepfake Vishing Attacks: The CEO Isn't Calling
Access File Artificial Intelligence, Cyber Security, Security Insights
Aug 5, 2025
Deepfake-as-a-Service (DaaS) Attacks: Your 2025 Guide to Defending Against Hyper-Realistic Social Engineering
Access File Cyber Security, Security Insights
Aug 4, 2025
EU Cyber Resilience Act 2025: A Survival Guide for C-Suites to Ensure Compliance and Avoid Crippling Fines
Access File Cyber Security, Security Insights
Aug 4, 2025
SBOM Implementation Guide 2025: How to Secure Your Software Supply Chain Now
Access File Cyber Security, Security Insights, Tech Innovations in Security
Aug 3, 2025
Beyond the Firewall: A 2025 Guide to OT Security for Critical Infrastructure Protection
Access File Artificial Intelligence, Cyber Security, Security Insights
Aug 3, 2025
The Imposter in the Machine: A 2025 C-Suite Guide to Combating AI-Powered Disinformation Attacks
Access File Cyber Security, Security Insights, Tech Innovations in Security
Aug 3, 2025
Post-Quantum Cryptography Readiness: A CISO's 2025 Guide to Surviving the Quantum Threat
Access File Artificial Intelligence, Cyber Security, Security Insights
Jul 23, 2025
Countering AI-Powered Social Engineering and Deepfake Attacks with Proactive Security
Access File Cyber Security, Security Insights, Tech Innovations in Security
Jul 21, 2025
Critical SharePoint Zero‑Day CVE‑2025‑53770 Actively Exploited
Access File Cyber Security, Physical Security, Security Insights
Jul 19, 2025
Physical Security: Strengthening Access Control in the Digital Age
Access File Cyber Security, Security Insights, Tech Innovations in Security
Dec 31, 2024
2024 Cybersecurity Review: A Year of Unprecedented Challenges
Access File Physical Security, Psychology, Security Insights
Dec 29, 2024