Database Query.
About Grab The Axe
Our methodology, leadership team, and the philosophy of the Cognitive Firewall.
Physical Security Assessments
Professional penetration testing and physical risk management for high-value facilities.
Behavioral Security Operations
Bridging the gap between clinical rigor and operational security strategy.
Executive Intensive
A high-performance coaching protocol designed for leaders in high-stakes environments.
Contact Terminal
Initialize communication for audits, media inquiries, or tactical consultations.

Rental Home Security: Lease-Friendly Ways to Deter, Delay, Detect, and Dispatch
Secure any rental home security, apartment, condo, or townhouse without drilling. Door, window, camera, and alarm tips using reversible "deter, delay, detect, dispatch" layers.

Client-Side Supply Chain Defense: Mastering Content Security Policy (CSP) for Modern Apps
Stop Magecart and formjacking attacks. A comprehensive 2000-word guide to implementing strict Content Security Policy (CSP), Subresource Integrity (SRI), and meeting PCI DSS v4.0 requirements

California DROP Tool: A New Era of Data Accountability
California's new DROP tool allows residents to scrub personal info from 500+ data brokers. Learn how this impacts privacy and security strategies

The Cyber Poverty Line: Why Elevating Small Vendor Security is a Strategic Enterprise Imperative
Small vendors pose a massive risk to enterprise security. Learn why The Cyber Poverty Line is the root cause and how strategic subsidies can fix it

Virtual Kidnapping Scams: The AI-Powered Terror Targeting Families and How to Verify Safety
AI voice cloning is fueling a surge in virtual kidnapping scams. Learn the psychology behind the fraud and the exact safe word protocols to protect your family.

API Security Guardrails: Implementing Fine-Grained Authorization to Neutralize BOLA Risks in 2026
Learn how to master API Security by implementing fine-grained authorization and OPA to neutralize BOLA risks and protect microservices in 2026.

End-of-Year Security Budgeting: Justifying Your 2026 Spend with a Data-Driven ROI
Struggling with your end-of-year security budgeting? Learn to build a data-driven business case that proves ROI and secures funding for 2026.

Holiday Shopping Scams 2025: A No-Nonsense Guide to Spotting AI-Powered Fakes
Worried about Holiday Shopping Scams 2025? Our no-nonsense guide helps you spot AI-powered fake stores and phishing attempts to protect your money.

Hostile Environment Awareness Training (HEAT): Essential Skills for High-Risk Corporate Travel
Protect your team abroad. Our guide on Hostile Environment Awareness Training covers essential skills for high-risk corporate travel to fulfill your duty of care.
The Psychology of Oversharing: How Social Media Habits Create Real-World Security Risks
Discover the psychology of oversharing and how your social media habits create security risks. Learn to protect your digital footprint from real-world threats.
Secure Coding for AI: Preventing Data Poisoning and Model Evasion in Your ML Applications
Learn practical secure coding for AI. Discover how to prevent data poisoning and model evasion in your ML applications with expert SDLC strategies.

Security Due Diligence in M&A: A Strategic Playbook for Seamless Integration
Unlock successful mergers by mastering security due diligence in M&A. Learn to identify hidden risks, harmonize cultures, and avoid costly post-deal surprises.
Android Zero-Days, NPM Malware, CISA Alerts & ICS Flaws – 12/02/2025
Critical security alert on two actively exploited Android zero-days. Details on a massive NPM malware attack, new CISA KEVs, and critical ICS vulnerabilities.

Hotel Room Security: A No-Nonsense Checklist for the Modern Traveler
Enhance your travel safety with this expert guide to hotel room security. Learn actionable steps and simple tools to protect yourself and your property.

Cyber Insurance Underwriting: Meeting the New Technical Requirements for Coverage in 2026
Struggling with cyber insurance underwriting? Learn the new technical requirements insurers demand for 2026 and how to prove your security maturity for coverage.
Malicious LLMs, Digital ID & Online Blackmail – 11/28/2025
Privacy threats today: Malicious LLMs empower hackers, UK digital ID raises concerns, and online blackmail targets kids. Stay secure with our analysis.
SFO Guidance, HIPAA Breach, Data Lawsuit – 11/28/2025
SFO updates compliance guidance; HIPAA breaches at Ennoble Care & Circa Health. Main Line Fertility settles data lawsuit. Stay compliant! - 11/28/2025

Supply Chain Attacks, Tomiris APT & CISA KEV Alert – 11/28/2025
Daily security brief on critical supply chain attacks in npm and PyPI, new Tomiris APT techniques, and a CISA KEV alert for an actively exploited vulnerability.

OpenAI Breach, APT Attacks & AI Jailbreaks – 11/27/2025
Daily security summary covering the OpenAI API data breach via Mixpanel, expanded Bloody Wolf APT attacks, and a new poetic jailbreak technique for LLMs.

OpenAI Breach, Student Privacy & EU Social Media Ban – 11/27/2025
Privacy news: OpenAI data breach, EFF fights student surveillance, EU proposes social media ban for minors. Stay informed on key privacy issues.

SFO Guidance, Anti-Smuggling, Greenwashing & FCA – 11/27/2025
Compliance update: UK SFO issues compliance guidance, Colombia strengthens anti-smuggling, Brazil tackles greenwashing, and FCA faces naming challenges. Stay compliant!

WebAssembly Security: Hardening the Next Generation of Cloud-Native and Edge Applications
A practical guide to WebAssembly security. Learn to harden WASM in cloud-native and edge apps, secure the host runtime, and manage a secure supply chain.
AI Fraud, GDPR Fine, & SEC Priorities – 11/26/2025
AI fraud surges, Croatia levies GDPR fine, & SEC releases 2026 priorities. Stay compliant with the latest regulatory and cybersecurity updates.
Iris Scan, ICE Face ID, Cybercrime & Huawei – 11/26/2025
Privacy threats today: Thai iris scan halt, ICE face recognition challenged, FBI warns of cybercrime surge, and Huawei surveillance concerns. Stay protected!

Deepfake Crisis Management: A Leader's Blueprint for a Post-Truth World
A leader's guide to deepfake crisis management. Learn to protect brand reputation, manage stakeholder psychology, and respond effectively in a post-truth world.
Porch Pirate Prevention: A No-Nonsense Guide to Securing Your Deliveries
Stop package theft with this no-nonsense guide to porch pirate prevention. Learn practical, field-tested strategies to secure your deliveries and protect your home.
Oracle Vulnerability, Coinbase Fine & Bribery Act – 11/24/2025
Oracle vulnerability actively exploited, Coinbase faces €21M fine, & UK sees landmark Bribery Act conviction. Stay informed on critical compliance updates.

Smart Toy Security: Protecting Your Kids from the Hidden Risks of Connected Playthings
Worried about your child's connected toys? Our guide to smart toy security helps you identify risks and protect your family from data leaks and surveillance.
Iberia Breach, AI Security Risks & Tool Updates – 11/23/2025
Critical security alert on the Iberia data breach from a vendor compromise. Analysis of weaponized file name flaws, AI safety risks, and key tool updates.
Sanctions, Dark Web Disclosure & Harm – 11/23/2025
Compliance update: US sanctions target Mexican casinos; US court equates dark web data leaks to harm. Stay compliant! - 11/23/2025

Living Off the Land Attacks: A Practitioner's Playbook for Detecting the Undetectable
Traditional security tools miss Living Off the Land attacks. This playbook provides technical, actionable threat hunting queries to find adversaries on your network.
Oracle Zero-Day, APT31 Attacks & WhatsApp Flaw – 11/22/2025
Critical Oracle zero-day is actively exploited. Read the latest on APT31 attacks against Russia, a massive WhatsApp data scraping flaw, and Qilin ransomware.

Security as a Business Enabler: Shifting from a Cost Center to a Competitive Advantage in 2026
Transform security from a cost center into a strategic asset. Learn how security as a business enabler drives growth, innovation, and trust in our 2026 outlook.

AI Cyberattack, Surveillance, Privacy Law – 11/21/2025
AI cyberattack surfaces! Surveillance concerns grow as police track protesters. Plus, new UK cyber laws & California health data privacy regulations.

WhatsApp Leak, AI Laws, Phishing Scams & Patent Rules – 11/20/2025
WhatsApp data leak! Plus, updates on AI laws, phishing scams, and changes to patent challenge rules. Stay informed with today's privacy and security briefing.

Fortinet Exploit, NIH Audit, Data Breach & EUDR – 11/19/2025
Critical Fortinet exploit, NIH security audit, healthcare data breach settlements, & EU deforestation directive updates. Stay compliant and informed.
IRS Data, ALPR Lawsuit, AI Listening & Nest Data – 11/19/2025
Privacy alert: IRS flight data access, ALPR lawsuit, AI in doctor's offices, & Google's Nest data collection. Stay informed on key privacy threats.

AI Phishing, Data Privacy, SEC, Fortinet – 11/18/2025
Stay ahead of compliance threats: AI phishing surge, data privacy law updates, SEC insights, & a critical Fortinet vulnerability. Read the full digest now!

Chrome Zero-Day, Azure DDoS, Data Breaches – 11/18/2025
Chrome zero-day exploit, Azure DDoS attack, and Princeton data breach lead today's security news. Stay informed about the latest threats and vulnerabilities.
Fortinet & Chrome Zero-Days, Cloudflare Outage – 11/18/2025
Critical security alerts for Fortinet & Chrome zero-days under active exploit. Today's summary covers the massive Cloudflare outage, new malware, and CISA advisories.
Healthcare Breaches, CCPA, AI Risk & GC Trends – 11/17/2025
Healthcare data breaches, new CCPA rules, AI investment risk, and general counsel trends. Stay informed on compliance and governance updates.
UNC1549 TTPs, Azure DDoS & Data Breaches – 11/17/2025
Analysis of Iran-nexus UNC1549 TTPs in the aerospace sector. Details on a massive 15 Tbps DDoS attack on Azure, plus new data breaches at Logitech and DoorDash.
Microsoft Zero-Day, Logitech Breach & Patch Tuesday – 11/16/2025
Microsoft's November Patch Tuesday fixes a critical zero-day under active exploit. Read the latest on the Logitech data breach and Coinbase disclosure claims.

SFDR 2.0, UK Businesses – 11/16/2025
SFDR 2.0 alert: Understand the implications of the leaked draft proposal for UK businesses. Stay informed on regulatory changes & compliance.
Akira, CMMC, Junk Fees & NPM Registry – 11/15/2025
Akira ransomware targets Nutanix VMs, CMMC requirements live, plus updates on junk fees laws and NPM registry attack. Stay compliant and secure!
GUARD Act, Data Breaches, AI & Privacy – 11/15/2025
Privacy news: GUARD Act threatens online privacy. Logitech data breach, Tate galleries applicant data leak, & AI-automated attacks. Stay informed!
XWiki Exploit, FortiWeb Attacks & Finger Malware – 11/15/2025
Critical alert on XWiki vulnerability CVE-2025-24893 (CVSS 9.8) under active exploit by RondoDox. Also covers FortiWeb attacks and new ClickFix malware.

Contractor Fraud Prevention: How to Spot and Avoid Home Improvement Scams
Learn essential contractor fraud prevention tips. We reveal the red flags, vetting checklists, and psychological tricks used in home improvement scams.
AI Cyberattacks, Fortinet Zero-Day & Akira Ransomware – 11/14/2025
Daily threat report: Chinese state actors leverage AI for cyberattacks, a critical Fortinet zero-day is actively exploited, and Akira ransomware targets Nutanix VMs.
The Diamond Model of Intrusion Analysis: A Practitioner's Guide to Threat Intelligence
Learn the Diamond Model of Intrusion Analysis to transform disconnected IOCs into actionable threat intelligence. This guide shows how to map campaigns and hunt adversaries.
runC Vulnerability, TP-Link Ban & Data Breach – 11/09/2025
Critical alert on runC container escape vulnerability. Analysis of the proposed U.S. ban on TP-Link routers and a major data breach at a Chinese infosec firm.

Public Event Security: A Situational Awareness Guide for Attendees
Learn essential public event security tips. Our guide covers situational awareness and emergency protocols to keep you safe in large crowds at concerts or festivals.

Mobile Malware, AI Security, Regulatory Compliance – 11/08/2025
Stay informed on mobile malware targeting Samsung, AI security concerns with Microsoft in UAE, and key regulatory compliance updates. Read the digest now!

Spyware, Car Surveillance, Firewall Flaws & Breaches – 11/08/2025
Privacy alert: New spyware targeting Samsung, car surveillance risks, Cisco firewall flaws exploited, and ID verification fueling data breaches. Stay informed!
VSCode Malware, AI Side-Channel & Windows 10 ESU – 11/08/2025
Security alert on GlassWorm malware in VSCode extensions. Microsoft reveals 'Whisper Leak' AI side-channel attack. Final warning for Windows 10 ESU enrollment.

Generative AI Ethics: Navigating the Line Between Corporate Intelligence and Digital Espionage
Explore the critical principles of Generative AI ethics. Learn to draw the line between competitive intelligence and digital espionage with a robust AI governance framework.
AI Ransomware, Cyberattack, Data Privacy – 11/07/2025
AI ransomware sneaks onto VS Code; US Budget Office hit by cyberattack. Plus, Europol data sharing & student data breach settlement. Stay informed!

Landfall Spyware, CBO Hack & Cisco Flaws – 11/07/2025
Critical security alerts on Landfall spyware exploiting a Samsung zero-day, a major CBO government hack, and active DoS attacks on Cisco firewalls. Stay informed.

API Fuzz Testing: A Practical Guide to Finding Security Flaws Before Attackers Do
Learn how API fuzz testing finds critical security flaws that traditional methods miss. Our guide helps developers implement fuzzing in their CI/CD pipeline.
DHS, Biometrics, Facial Recognition & Data Breach – 11/06/2025
DHS biometric data seizure, CBP facial recognition app, & Hyundai data breach. Stay informed on the latest privacy threats and data security news.
Sandworm Wipers, Cisco Flaw, & SonicWall Breach – 11/06/2025
Daily security brief on Russia's Sandworm wiper attacks, a critical Cisco UCCX flaw allowing root access, and SonicWall's state-sponsored breach confirmation.
Zero-Day, ChatGPT Bugs, FINRA Fine & Data Breaches – 11/06/2025
Zero-day exploit targeting Japan, ChatGPT security bugs, a $10M FINRA fine, and healthcare data breaches lead today's compliance news. Stay secure and compliant.

Verbal De-escalation Techniques: Empowering Your Customer-Facing Teams
Learn actionable verbal de-escalation techniques to empower your teams, reduce conflict, and protect your business. A human-centric guide for leaders.

Android Malware, Data Breach, EU Surveillance – 11/05/2025
Android malware impacts millions, California tightens breach notification, and EU officials' surveillance data is for sale. Stay informed on key privacy threats.

WordPress Exploit, Ransomware & AI Compliance – 11/05/2025
Critical WordPress exploit, ransomware surge in Europe, and AI compliance risks. Stay ahead with the latest insights and protect your organization now.

Mergers and Acquisitions Cybersecurity: The Unseen Risks in a Billion-Dollar Deal
Discover the unseen risks in M&A deals. Our guide to mergers and acquisitions cybersecurity due diligence helps you avoid costly liabilities and protect your investment.
ICS Vulnerabilities, WordPress Exploit & Russian Malware – 11/04/2025
Critical ICS vulnerabilities (CVSS 10.0) and an actively exploited WordPress flaw lead today's threats. Get details on new Russian malware tactics and data breaches.
OpenAI Backdoor, Healthcare Breach & Ransomware – 11/04/2025
Compliance digest: OpenAI backdoor malware, healthcare data breach, and ransomware indictments. Stay informed on critical security & regulatory updates.
Racist Policing, Ring Privacy, App Censorship & Payroll Scams – 11/04/2025
Privacy threats today: Racist policing via surveillance, Ring's privacy risks, app censorship concerns, & payroll scams. Stay secure with our analysis.

Operational Technology Security: Applying the Purdue Model for ICS Defense
A technical guide to Operational Technology Security. Learn to apply the Purdue Model for robust ICS and SCADA defense through proper network segmentation.

Data Breaches, AI Manipulation & User Consent – 11/03/2025
Privacy threats today: University of Pennsylvania data breach, AI manipulation tactics, and user consent guidance. Stay informed and protect your data!
DeFi Heist, Insider Threats & AI Malware – 11/03/2025
Daily threat report: Over $120M stolen in a DeFi heist, DOJ indicts ransomware negotiators in an insider plot, and new AI-powered malware uses OpenAI for C2.
Travel Security Essentials: A Practical Guide to Staying Safe Abroad
Enhance your travel security with our practical guide. Learn to protect your data, wallet, and self from common threats abroad. Essential tips for every traveler.

Family Cyber Safety Plan: A Step-by-Step Guide to Setting Digital Ground Rules with Your Kids
Feeling lost about your kids' online world? Our guide provides a step-by-step family cyber safety plan to reduce conflict and build lasting digital trust.

C-UAS Legalities for Corporations: Navigating the FAA and FCC Rules Before You Deploy Counter-Drone Tech
A critical overview of C-UAS legalities for corporate leaders. Understand the FAA and FCC rules before you deploy counter-drone tech to avoid massive fines.
Data Breach, AML Reform, & AI Governance – 10/28/2025
Key compliance updates: Major data breach, UK AML reform details, and AI governance insights. Stay informed on critical risks & regulatory changes.
Social Engineering, Malware, 2FA & AI Strategy – 10/28/2025
Stay ahead of privacy threats: Social engineering credit card scams, Android malware, 2FA re-enrollment on X, and the EU's new AI strategy. Read the details!
TEE.Fail Attack, Qilin Ransomware, CISA Alerts & BlueNoroff – 10/28/2025
Critical TEE.Fail attack extracts secrets from Intel, AMD, and NVIDIA CPUs. CISA adds exploited Dassault flaws to KEV catalog. Read today's top security threats.

Ransomware, Data Breach, & FATF Updates – 10/27/2025
Stay ahead of compliance threats: Linux ransomware targets Windows, HIPAA breach settlement, and FATF AML updates. Expert analysis for October 27, 2025.
Spyware, AI Strategy, Data Privacy – 10/27/2025
Stay informed: Spyware attacks, EU AI strategy & data privacy tips. Get the latest on critical privacy threats and regulations in our daily summary.
WSUS Flaw, Qilin Ransomware & Italian Spyware – 10/27/2025
CISA orders immediate patching for a critical WSUS vulnerability under active exploit. Get the latest intelligence on Qilin ransomware TTPs and new spyware.

CoPhish, Hospital Breach & FTC Scams – 10/26/2025
Privacy alert: New CoPhish attack, hospital breach exposes patients. Plus, FTC warns of Amazon scams and identity theft risks. Stay protected!

The Ethics of AI in Predictive Security: Balancing Proactive Defense with the Dangers of Algorithmic Bias
Explore the complex ethics of AI in security. Learn to balance proactive defense with the risks of algorithmic bias and implement responsible AI governance.
CIPA, Biometrics, UN Cybercrime & Privacy Tips – 10/25/2025
Privacy news: CIPA faces criticism, Philippines bans biometric data sales, EFF warns on UN Cybercrime Convention. Plus, tips to boost your privacy today!
CoPhish Attack, AI Browser Risks & OAuth Threats – 10/25/2025
Daily security brief on the new 'CoPhish' attack stealing OAuth tokens, major security risks in AI browser agents, and growing AI-powered surveillance threats.

Windows Patch, Pay Transparency, AI Act & FCPA – 10/25/2025
Critical Windows patch, NJ pay transparency rules, AI Innovation Act impact, & FCPA updates. Stay ahead of compliance challenges. Read more!

Industrial Control System (ICS) Security: A No-Nonsense Primer for Securing PLCs and SCADA Networks
A direct, no-nonsense primer on Industrial Control System Security. Learn practical steps to protect your PLCs and SCADA networks from cyber-physical threats.
AI, Surveillance, Data Brokers & Breach Laws – 10/24/2025
AI surveillance in schools, data broker expansions, & breach notification law updates. Stay informed on key privacy threats and regulations.

Cyber Risk, HIPAA & AI Policy Updates – 10/24/2025
Stay ahead: Cyber risk guidance, HIPAA breach, and AI policy updates. Key compliance insights for October 24, 2025. Protect your organization now.
WSUS Vulnerability, WordPress Exploits & GlassWorm Worm – 10/24/2025
Critical WSUS vulnerability (CVE-2025-59287) is actively exploited, prompting emergency Microsoft patches. Also covers WordPress plugin attacks and a new worm.

The Security of Aging in Place: A Guide to Smart Home Tech and Physical Safety for Seniors
Discover how to ensure the security of aging in place for your loved ones. Our guide covers smart home tech and physical safety upgrades for senior independence.

F5 Breach, AI Spoofing, Data Transparency – 10/23/2025
F5 breach alert: Nation-state attack compromises updates. Plus, AI spoofing risks and health app data transparency issues. Stay informed and secure!
Lanscope Flaw, Adobe Exploits & Lazarus Group – 10/23/2025
Critical alert on an exploited Lanscope flaw. Analysis of active Adobe Commerce attacks, Lazarus Group's defense targets, and new ICS advisories from CISA.
Privacy Laws, Data Breach, Meta Bots – 10/18/2025
Privacy updates: California's new laws, ICO's Capita fine, Meta's bot safeguards, & EFF's privacy tips. Stay informed on data protection and online safety.

Malicious Code Forensics: A Practitioner's Guide to Reverse Engineering Malware from Compromised IoT Devices
Master malicious code forensics for IoT. This guide covers firmware extraction, ARM malware analysis, and building a safe lab to reverse engineer threats.
Surveillance, Data Breach & EFF Lawsuit – 10/17/2025
EFF sues over online surveillance, Zendesk email bombs, unencrypted satellite data & more. Stay informed about today's critical privacy threats.
Ransomware, Data Breach, NY DFS, & Password Risks – 10/17/2025
Ransomware surge, data breach settlements, and NY DFS cybersecurity fines lead today's compliance news. Password managers under attack. Stay informed and secure!

Vacation Rental Security: A Traveler's Checklist for Spotting Hidden Cameras and Securing Your Airbnb
Don't risk your privacy. Our expert checklist for vacation rental security helps you find hidden cameras and secure any Airbnb for peace of mind.

Cyber Threats, Healthcare Breach, & AML Updates – 10/16/2025
Stay ahead of cybersecurity threats with updates on healthcare breaches, AML regulation changes, and key compliance alerts. Read our summary now!
EtherHiding, Phishing, Adobe Flaw & Data Breach – 10/16/2025
Privacy threats today: North Korean hackers use EtherHiding, phishing targets password managers, Adobe flaw exploited, and Capita fined for data breach. Stay informed!
The Digital Identity Paradox: Reconciling Privacy and Security in the Age of Self-Sovereign Identity (SSI)
Explore the Digital Identity Paradox and how Self-Sovereign Identity (SSI) solves data liability, reduces corporate risk, and rebuilds customer trust.
Apple Bounty, Android Attack, Surveillance & MANGO Breach – 10/15/2025
Apple enhances bug bounty, Android 'Pixnapping' steals MFA, surveillance empire exposed & MANGO data breach. Stay informed on top privacy threats.
Data Breach, CCPA, Oracle Attack & Patch Update – 10/15/2025
Data breach at Harvard, new CCPA rules, and a massive Microsoft patch update lead today's compliance news. Stay informed on the latest threats and regulations.
Geofencing for Asset Protection: A No-Nonsense Guide to Tracking and Securing High-Value Equipment
Learn how geofencing for asset protection stops theft and unauthorized use. Our no-nonsense guide covers implementation, integration, and real-world results.
Data Breach, AI Surveillance & Student Tracking – 10/14/2025
Privacy alert: Data breaches impact healthcare, LinkedIn lawsuits, AI surveillance, & Microsoft student tracking. Stay informed on key privacy developments.
Sanctions, Data Breach, Warfare & UK Policy – 10/14/2025
Stay compliant: UK sanctions list update, healthcare data breach settlements, Russian hybrid warfare risks, & new UK pension policy. Read the full summary.
Windows Zero-Days, Patch Tuesday & Android Attacks – 10/14/2025
Critical Patch Tuesday alert: Microsoft fixes 172 flaws and 6 zero-days as Windows 10 support ends. Get analysis on new Android attacks and CISA KEV updates.

Smart Building Security: Protecting Your Facility's HVAC, Lighting, and Elevator Systems from Cyber-Physical Threats
A technical guide to smart building security. Learn to protect HVAC, lighting, and elevator controls from cyber-physical threats targeting your BAS and OT.
Data Breaches, Quantum Threat & DC BEST Act – 10/13/2025
Compliance digest: Data breach settlements, quantum computing threats, D.C.'s BEST Act, & critical infrastructure data sprawl. Stay informed on key risks.
Oracle Zero-Day, Android 2FA Theft & IE Exploit – 10/13/2025
Daily security brief on a critical Oracle zero-day flaw requiring an emergency patch, a new 'Pixnapping' attack stealing Android 2FA codes, and MS IE mode exploits.
Student Data, AI Ethics, Data Breaches & Regulations – 10/13/2025
Privacy alert: Microsoft student data tracking, AI ethics concerns, data breach impacts, and new privacy regulations. Stay informed and secure your data.

Converged Security Operations Center: The Strategic Business Case for Unifying Cyber and Physical SOCs
Discover the strategic business case for a Converged Security Operations Center. Unify cyber and physical security to reduce risk and boost efficiency.

Securing Remote and Off-Grid Properties: A Practical Guide for Cabins, Farms, and Vacation Homes
A practical guide to securing remote properties. Learn to protect your cabin, farm, or vacation home with low-tech deterrents and modern off-grid security.
Edge Vulns, Botnet Exploits, & Regulations – 10/11/2025
Edge vulns exploited by RondoDox botnet & AI browser agent security gaps addressed. Plus: Victorian psychosocial regulations & NCAA gambling policy updates.
SonicWall VPN Attacks, LockBit Tactics & Apple Bounties – 10/11/2025
Critical alert on widespread SonicWall VPN compromise. Analysis of LockBit ransomware weaponizing DFIR tools and Apple's increased bug bounty rewards for exploits.

Zero-Day Exploit, Data Scraping & Foster Youth Risks – 10/11/2025
Zero-day exploit in Gladinet, data scraping privacy clash, and identity theft risks for foster youth. Stay informed on today's top privacy threats.

Container Escape Vulnerabilities: A Technical Deep Dive for DevOps and Cloud Security Teams
Learn to mitigate critical container escape vulnerabilities. Our deep dive covers kernel exploits, misconfigurations, and modern hardening like gVisor and seccomp.
The Psychology of Quishing: Why QR Code Scams Exploit Our Brain's Trust in Technology
Explore the psychology of quishing and why QR code scams are so effective. Learn how they exploit cognitive biases and how to protect your organization.

AML Failures, AI Law, Data Breach, FCA Scheme – 10/08/2025
AML failures in Europe, Vietnam's AI law, data breach at Harris Health, & FCA redress scheme. Stay compliant with the latest security updates.
ALPR Abuse, AI Influence, Discord Breach – 10/07/2025
Privacy alert: ALPR misuse in Texas, AI influence campaign, & Discord data breach exposing IDs. Plus, spyware in UAE & CISA guidance updates.

Security Program from Day One: A Startup Founder's Guide to Building a Resilient Company
Build a resilient startup with our founder's guide. Learn to implement a Security Program from Day One, turning cybersecurity into a competitive advantage.
Data Breach, GDPR, Cyber Tech & FinCrime – 10/06/2025
Stay ahead: Data breach settlement, GDPR training insights, Chinese cyber tech exploitation, and AI in FinCrime prevention. Read the full compliance digest.
Oracle Zero-Day, Clop Attacks & GoAnywhere Exploit – 10/06/2025
Critical Oracle zero-day (CVE-2025-61882) actively exploited by Clop ransomware. Get details on the GoAnywhere MFT bug, Red Hat data breach, and other top threats.

eBPF for Security: A Practitioner's Guide to Cloud-Native Threat Detection
Unlock kernel-level visibility in cloud-native environments. Our practitioner's guide to eBPF for security covers the tools and techniques for next-gen threat detection.
Cybercriminal Tactics, Nation-State Hackers – 10/05/2025
Understand cybercriminal and nation-state hacker tactics. Learn how they operate in this Dark Reading virtual event. Stay ahead of threats! - 10/05/2025

Zimbra Flaw, ParkMobile Breach & Data Scams – 10/05/2025
Zimbra zero-day exploit, ParkMobile's breach settlement, and a rise in data scams. Stay informed about today's top privacy threats and how to protect yourself.

Zimbra Zero-Day, Gov Cloud Loss, & ParkMobile Breach – 10/05/2025
Critical alert on Zimbra zero-day exploit using iCalendar files. Analysis of the ParkMobile data breach settlement and a catastrophic government cloud data loss.

Digital Legacy Planning: A Compassionate Guide to Securing Your Family's Online Life After You're Gone
Our compassionate guide to digital legacy planning helps you protect online accounts, photos, and assets, preventing a digital mess for your loved ones.
Data Breaches, Tile Vulnerability & AI Risks – 10/04/2025
Critical data breaches at Discord & Renault/Dacia, Tile tracker vulnerabilities exposed. Plus, AI risks & FTC scam warnings. Stay secure!
Export Controls, AI Safety, Lapsus$ & Cybersecurity – 10/04/2025
Export control expansion, CA's AI safety law, and Lapsus$’s return highlight today's compliance risks. Plus, cybersecurity protection expiration analysis.

Palo Alto Scans, Discord Breach & AI CometJacking – 10/04/2025
Critical alert on massive Palo Alto Networks scans indicating reconnaissance. Details on the Discord data breach, new AI CometJacking attack, and other key security risks.

Salesforce Leak, Cyberattacks & FTC Shutdown – 10/04/2025
Salesforce leak threat, rising cyberattack costs, & FTC shutdown plan: Stay ahead of critical compliance issues with our intelligence digest. Read more now!
AI Regulation and Security: A C-Suite Guide to Navigating the 2026 Legislative Minefield
A C-suite guide to AI regulation and security. Understand the EU AI Act and adapt your corporate strategy to avoid massive fines and reputational damage by 2026.
ICE Tracking, CometJacking, Salesforce Leak – 10/03/2025
Privacy threats today: ICE's mass phone tracking, CometJacking email theft, Salesforce data leak, & FTC action on child data. Stay secure & informed.
Salesforce Breach, Oracle Flaw & CISA Alert – 10/03/2025
Daily security summary on the massive Salesforce breach by Scattered Spider, Oracle EBS flaws exploited by Clop, and a new CISA KEV alert. Stay informed.
Memory-Safe Languages: How Rust is Eliminating Entire Classes of Security Vulnerabilities
Discover how memory-safe languages like Rust prevent 70% of high-severity vulnerabilities. Learn to eliminate entire classes of bugs like buffer overflows.

Data Breaches, Apple Backdoor & Android Spyware – 10/02/2025
Major data breaches at WestJet & Motility, UK demands Apple backdoor, & new Android spyware. Stay informed about today's top privacy threats.
Oracle Extortion, Red Hat Breach & CISA KEVs – 10/02/2025
Daily threat report on the Clop-linked Oracle extortion campaign, Red Hat's GitLab breach, CISA's new KEVs, and a critical RCE bug in DrayTek Vigor routers.
Gray Man Theory: The Art of Blending In for Everyday Personal Safety
Feeling anxious in public? Learn the Gray Man Theory, a practical method for blending in and avoiding unwanted attention. A no-nonsense guide to personal safety.

Data Breach, GDPR, & SEC Compliance – 10/01/2025
Stay ahead of compliance: Data breach in Florida, GDPR updates, SEC guidance, and China's new cyber incident reporting rules. Read the latest now!
Data Breaches, OpenShift Flaw & China APT – 10/01/2025
Daily security report: Major data breaches at WestJet and Allianz impact millions. A critical Red Hat OpenShift AI flaw allows full takeover. New China APT found.

Return-to-Office Security Risks: The Converged Threats Created by Your Hybrid Work Mandate
Discover the hidden Return-to-Office Security Risks. We cover the converged threats—cyber, physical, and psychological—created by hybrid work mandates.

VMware Exploit, Linux Flaw, EU Chat Control – 09/30/2025
VMware zero-day exploit and Linux Sudo flaw require immediate attention. EU's Chat Control proposal sparks privacy concerns. CCPA updates included.
VMware Zero-Day, CISA Alerts & Cisco Flaws – 09/30/2025
Critical VMware zero-day exploited by Chinese hackers since Oct 2024. CISA issues urgent patch orders for Fortra and Sudo flaws. 50k Cisco firewalls at risk.

Confidential Computing Implementation: A Developer's Guide to Protecting Data-in-Use with Secure Enclaves
A developer's guide to practical Confidential Computing Implementation. Learn to protect data-in-use with secure enclaves like Intel SGX and AMD SEV-SNP.
AI Vulnerability, Data Breach & Ransomware – 09/29/2025
AI vulnerability in Notion, Harrods data breach, & Akira ransomware bypass MFA. Stay informed about the latest privacy threats and security breaches.

CISA KEV, SonicWall Attacks, JLR Breach & AI Threats – 09/29/2025
CISA adds 5 known exploited vulnerabilities to its KEV catalog. Analysis of Akira ransomware hitting SonicWall VPNs, the JLR breach, and new AI-driven phishing.
Data Breach, Supply Chain, AML Reforms & DPO – 09/29/2025
Compliance updates: Data breach at Veradigm, FASCA order on Acronis, AML reforms, and guidance for DPOs in the UK. Stay informed on key compliance risks.
Akira Ransomware, MFA Bypass & AI Security – 09/28/2025
Critical alert on Akira ransomware bypassing MFA on SonicWall VPNs. This security digest covers the latest threat intelligence, major incidents, and AI's role in attacks.
DNA, COPPA, Ransomware & Radicalization – 09/28/2025
Privacy digest: DHS DNA collection, Akira ransomware bypasses MFA, Disney's COPPA fine, and online radicalization trends. Stay informed on today's key threats.
Nursery Hacking, AML Supervision & Astute LXP – 09/28/2025
Nursery hacking incident, AML regulatory changes, and Astute LXP updates. Stay informed on key compliance and security developments.
Layered Critical Infrastructure Defense: A Practical Strategy for Protecting Geographically Dispersed Assets
Learn a practical strategy for Layered Critical Infrastructure Defense. Move beyond simple fences to protect vast assets like pipelines and power grids.

PlugX Malware, Oyster Backdoor & NPM Threats – 09/27/2025
Critical threat intelligence digest for 09/27/2025. In-depth analysis of China-linked PlugX malware, Oyster backdoor in fake Teams installers, and NPM backdoors.

AI-Induced Alert Fatigue: Managing the Psychological Strain of Human-Machine Teaming in the Modern SOC
Overwhelmed by AI-generated alerts? Learn to manage AI-induced alert fatigue, reduce SOC burnout, and build a resilient human-machine security team.

GoAnywhere Flaw, Cisco Exploits & LockBit Variant – 09/26/2025
Critical GoAnywhere MFT zero-day (CVSS 10.0) under active exploit. Get the latest on Cisco firewall attacks, a new dangerous LockBit variant, and other top threats.

Securing OT-Cloud Integration: A Practical Playbook for Bridging the Air Gap Without Compromising the Plant Floor
Learn how to bridge the air gap safely with our guide on securing OT-cloud integration. Protect your plant floor while leveraging IIoT data analytics.

Cisco Zero-Days, Shai-Hulud Worm & CISA Alerts – 09/25/2025
Critical alert on Cisco zero-day vulnerabilities under active exploit. Details on the CISA emergency directive, 'Shai-Hulud' npm worm, and major data breaches.

Offensive AI Cyber Operations: The Strategic and Ethical Dilemmas of AI-vs-AI Warfare
Explore the strategic and ethical dilemmas of Offensive AI Cyber Operations. A guide for leaders facing the reality of AI-vs-AI cyber warfare.

Cisco Zero-Day, BRICKSTORM Malware & Supermicro Flaws – 09/24/2025
Critical security alert: A Cisco IOS zero-day is under active exploit. Get analysis on this threat, the BRICKSTORM espionage backdoor, and persistent Supermicro flaws.

Corporate Drone Espionage: Recognizing and Countering Aerial Surveillance Threats to Your Facility
Learn to counter corporate drone espionage. This guide covers detecting aerial surveillance, legal response, and hardening your facility against this growing physical security threat.

NPM Supply Chain, GeoServer Exploit & CISA Alerts – 09/23/2025
Critical security update on the widespread NPM supply chain compromise (Shai-Hulud worm) and CISA's alert on an exploited GeoServer vulnerability. Read more now.

Automated DevSecOps Governance: Integrating VEX and SBOMs into Your CI/CD Pipeline for Real-Time Risk Triage
Tired of vulnerability alert fatigue? Learn how to implement Automated DevSecOps Governance by integrating VEX and SBOMs to focus only on exploitable risks.

Airport Ransomware, Stellantis Breach & AI Risks – 09/22/2025
Get the latest on the ransomware attack disrupting European airports, the Stellantis data breach, a critical Entra ID flaw, and new AI security risks in today's digest.

Insider Threat Psychology: Why Burnout and Disengagement Are Your Biggest Security Vulnerabilities
Explore insider threat psychology and learn why employee burnout is your biggest security risk. Discover strategies to build a more resilient workforce from within.

Entra ID Flaw, Airport Cyberattack & AI Security – 09/21/2025
Critical Microsoft Entra ID flaw could allow tenant hijacking. Also covers a major airport cyberattack, Notion AI data leak risks, and DPRK malware campaigns.

Post-Quantum Cryptography (PQC) Migration: Charting the Strategic and Ethical Roadmap for a Quantum-Resilient Enterprise
A strategic and ethical guide for CISOs and board members on Post-Quantum Cryptography (PQC) Migration. Learn to navigate the risks and build a quantum-resilient enterprise.

AI Malware, Entra ID Flaw, & ShadowLeak Vuln – 09/20/2025
Security digest for 09/20: Critical Microsoft Entra ID flaws, new GPT-4 powered malware 'MalTerminal,' and a zero-click ShadowLeak flaw in OpenAI's agent.

Combating Security Fatigue: A Human-Centric Blueprint for Building Resilient and Engaged Employees
Tired of employees ignoring security warnings? Learn how to combat security fatigue with a human-centric approach that builds a resilient and engaged team.

GoAnywhere Flaw, Russian APTs & Scattered Spider – 09/19/2025
Critical GoAnywhere MFT vulnerability (CVSS 10.0) requires immediate patching. Also, Russian APTs Turla and Gamaredon collaborate on new attacks against Ukraine.
Drone Penetration Testing: How Adversaries Use Commercial Drones to Case Your Facility
Your fences and cameras are blind to aerial threats. Learn how a drone penetration test exposes critical vulnerabilities from off-the-shelf commercial drones.

Scattered Spider Arrest, Chrome Zero-Day & AI Threats – 09/18/2025
Daily security digest covers the arrest of a Scattered Spider hacker, a new Chrome zero-day under active exploit, and a zero-click vulnerability in OpenAI's ChatGPT.

GraphQL Security Blind Spots: A Developer's Playbook for Preventing Data Exposure and Resource Exhaustion Attacks
Discover how to fix critical GraphQL security vulnerabilities. This developer's playbook covers data exposure, DoS attacks, and building secure-by-design APIs.

Salesforce Breach, JLR Production Halt & SonicWall Alert – 09/17/2025
Stay informed on critical security threats from 09/17/2025. Details on the massive ShinyHunters Salesforce data breach, JLR production halt, and a SonicWall alert.

Executive Liability in Cybersecurity: A C-Suite Guide to Navigating Post-2024 SEC Enforcement Actions
A guide for C-Suite leaders on navigating SEC enforcement and personal liability. Understand the new rules and protect your career from governance failures.
NPM Worm, JLR Cyberattack, & Mobile Zero-Days – 09/16/2025
Critical security alert: A self-replicating NPM worm is fueling a massive supply chain attack. Also covered: Jaguar Land Rover's cyberattack shutdown & zero-days.

The Hybrid SOC Team: Managing the Psychology of Human-AI Collaboration in Security Operations
AI is shaking up security operations. Learn to manage the psychology of The Hybrid SOC Team to build trust, boost morale, and improve threat detection.

FBI Salesforce Warning, Ransomware & Rowhammer Bypass – 09/15/2025
Critical security alert: The FBI warns of active attacks on Salesforce. Read analysis on new ransomware hitting schools, a Rowhammer bypass for DDR5, and more.

Securing Distributed Energy Grids: A No-Nonsense Physical Security Blueprint for Solar and Battery Farms
Learn the no-nonsense blueprint for securing distributed energy grids. This guide covers physical security for solar and battery farms against modern threats. Protect your assets.

Salesforce Threats, VoidProxy Phishing & AI Risks – 09/14/2025
FBI warns of hackers stealing Salesforce data via UNC6040/UNC6395. Also, new VoidProxy PhaaS targets M365/Google, and AI chatbots spread more false info.

CNAPP Optimization with AI: A Technical Playbook for Automating Cloud Threat Response
Unlock your cloud's potential with our technical playbook on CNAPP Optimization with AI. Learn to automate threat response and stop analyst alert fatigue for good.

FBI Alert, Salesforce Security & Threat Actors – 09/13/2025
FBI issues a critical alert on threat actors UNC6040 and UNC6395 targeting Salesforce platforms for data theft. Read our latest intelligence digest for details.

Digital Sovereignty Imperative: A 2025 Strategic Guide for US Corporations Navigating Global Data Laws
By 2025, more than 70 countries will enforce some form of data localization law. This isn't a distant forecast. It's the immediate reality for every US

Exploited Vulns, HybridPetya Ransomware & Spyware – 09/12/2025
CISA warns of an actively exploited RCE flaw and Samsung patches a zero-day. Get the latest on the new HybridPetya ransomware and nation-state spyware campaigns.

Physical Security Since 9/11: A 24-Year Retrospective on Protecting Public Spaces
A 24-year retrospective on physical security since 9/11. We examine the lasting changes, from standoff distance to CPTED, and what they mean today.

SonicWall Exploits, VMScape Attack, Siemens Flaws, and Rising Spyware Risks
Top threats on Sept 11, 2025: Akira ransomware hits SonicWall, VMScape attack leaks hypervisor data, Siemens flaws, spyware surge, and more.

Digital Twin Security: A 2025 Playbook for Protecting Critical Infrastructure
A technical playbook on Digital Twin Security for CISOs in critical infrastructure. Learn to protect cyber-physical systems from data poisoning and sabotage.

Kerberoasting Attacks, Jaguar Land Rover Breach, and Malicious NPM Package
Stay informed on the latest cybersecurity threats. This article breaks down the recent Jaguar Land Rover data breach, the widespread npm supply chain attack, and the persistent threat of Kerberoasting attacks. Understand the risks and protect your organization from these evolving cyberattacks.
Fine-Grained Authorization: A Technical Guide to Implementing Modern Access Control for Microservices
Move beyond RBAC. This technical guide covers implementing modern, fine-grained authorization for microservices using ReBAC, OPA, and OpenFGA. Secure your apps.
Behavioral Security Training: Moving Beyond Phishing Clicks to Create Real Culture Change
Traditional security awareness is stuck in a compliance-first mindset. It’s a checkbox item designed to satisfy auditors, not to inspire people. The result is
Hostile Vehicle Mitigation: Practical Design and Implementation Beyond Simple Bollards
Effective Hostile Vehicle Mitigation is more than just bollards. Learn to design practical HVM strategies that balance robust security with aesthetics.

Cyber-Physical Security AI: When Your Hacked Security Robot Becomes the Insider Threat
By 2025, Gartner predicts that 30% of major corporate breaches will involve the compromise of a cyber-physical system. That's a staggering jump from less than

VEX in DevSecOps: How to Use the Vulnerability Exploitability eXchange to Prioritize Real Threats
Stop chasing ghost vulnerabilities. Learn to integrate VEX in DevSecOps to filter SBOM noise, prioritize real threats, and secure your CI/CD pipeline.
Private C-UAS Deployment: A No-Nonsense Guide to Legally Protecting Your Facility from Drones
Considering private C-UAS deployment? This guide covers the complex FAA/FCC regulations and legal risks for protecting your facility from drone threats.
AI Social Engineering: How Attackers Weaponize Psychology and How to Build Human Resilience
Attackers now use AI social engineering to exploit human psychology. Learn how to spot hyper-personalized threats and build cognitive resilience in your team.

Autonomous AI Threats: The New Frontier of Corporate Espionage and How to Prepare Your Defenses
Are your traditional security models prepared for an adversary that thinks, adapts, and executes without human oversight? We are on the precipice of a new era
SOC Analyst Burnout: A Labor Day Call to Action to Protect Your Human Firewall
Tackle SOC analyst burnout to protect your organization. Learn human-centric strategies to reduce turnover and transform operational risk into cyber resilience.
Predictive Analytics for Physical Security: Using Data to Anticipate and Mitigate Threats
The core problem with traditional security is that it's pattern-blind. A guard can't see the connection between a series of failed access attempts at a side

Service Mesh Security: A Deep Dive into mTLS and Access Control for Microservices
A deep dive into Service Mesh Security. Learn how to secure microservices with automated mTLS, fine-grained access control, and Zero Trust principles.
Leading Through a Breach: A Psychological Playbook for Maintaining Team Morale and Customer Trust
What's the most damaging, long-term cost of a security breach? It isn't the ransom paid or the regulatory fines. It's the loss of your people. In the year
The Philosophy of Secure by Design: Moving Beyond Compliance to Create Inherently Resilient Systems
Move beyond brittle, compliance-first security. Learn the philosophy of Secure by Design to build inherently resilient systems and reduce costs by 100x.
Access Control Credential Cloning: A Real-World Threat Assessment and Mitigation Guide
The root of the problem lies in the technology itself. For decades, the standard for access control was the 125kHz proximity card. Think of common cards like

Automated Threat Hunting: Integrating SOAR and AI to Proactively Find Hidden Adversaries
Learn how to implement automated threat hunting using SOAR and AI. Go beyond reactive alerts and proactively find adversaries already in your network.

Security Culture Metrics: How to Quantitatively Measure and Improve Your Human Firewall
Move beyond click-rates. Learn how to use security culture metrics to prove ROI, reduce human risk, and build a stronger, quantifiable human firewall.
The Board's Fiduciary Duty in Cybersecurity: Interpreting the SEC's Rules One Year Later
One year after the new SEC rules, understand your board's fiduciary duty in cybersecurity. Learn key questions to ask and how to mitigate personal liability.

Counter-Drone Technology for Critical Infrastructure: A Practical Guide to Detection and Mitigation
Ignoring the drone threat is no longer an option. The challenge isn't just the physical risk. It's navigating the complex technology and the even more complex
Securing LLM APIs: A Technical Playbook for Preventing Prompt Injection and Data Exfiltration
For developers and security engineers, this isn't just another item on a checklist. It's a fundamental shift in how we must approach application security.
The Psychology of CEO Fraud: Why Executives Are Uniquely Vulnerable to Sophisticated Social Engineering
Discover the psychology of CEO fraud and why leaders are prime targets. Learn how attackers exploit authority and urgency, and how to build effective defenses.
Cognitive Biases in Cybersecurity: How Mental Shortcuts Create Security Blind Spots for Your SOC Team
Your Security Operations Center (SOC) is a high-stakes, high-pressure environment. In this setting, the human brain, brilliant as it is, relies on mental
CNAPP Implementation: A Practical Guide to Unifying Cloud Security from Code to Production
Struggling with fragmented cloud tools? This guide offers a practical CNAPP implementation strategy to unify security from code to production. Learn more.

Geopolitical Cyber Risk: A 2025 C-Suite Guide to Navigating Digital Sovereignty and Data Localization
A C-suite guide to navigating geopolitical cyber risk. Learn how digital sovereignty and data localization laws reshape global business and how to lead.

Ballistic Protection Standards: A No-Nonsense Guide to NIJ Levels for Corporate Facilities
Confused by NIJ levels? Our guide to ballistic protection standards helps you choose the right protection for your facility and avoid costly mistakes.

Modern Executive Protection: Blending Physical Security with Digital Threat Intelligence
The days of defining executive protection by the number of 'bodyguards' in a motorcade are over. That model is a relic. It’s a reactive strategy in an era

SOC Analyst Burnout: Psychological Strategies for Building Resilience in Your Security Team
Tackle SOC Analyst Burnout head-on. Discover psychological strategies to build resilience, reduce turnover, and strengthen your security team's mental health.
Insider Threat Program Development: A Guide to Detecting and Mitigating Internal Risks
Learn the essentials of Insider Threat Program Development. A guide for CISOs to build a program that mitigates risk without creating a 'Big Brother' culture.

Zero Trust Architecture Implementation: A Phased Approach to Eliminating the Perimeter
For 20 years, I’ve watched security leaders build bigger walls, deeper moats, and stronger gates. We called it “defense in depth.” But today, that
De-escalation Training for Employees: A Proactive Strategy for Workplace Violence Prevention
Discover how de-escalation training for employees can prevent workplace violence. Learn key techniques to empower your team and create a safer environment.

API Security Best Practices: Why Your APIs Are the New Shadow IT and How to Protect Them
Without a complete inventory, you're flying blind. Achieving this visibility is the foundational step for all other API security best practices.

AI-Powered Physical Security: The Rise of Autonomous Surveillance and Predictive Analytics
Your security team is watching hundreds of video feeds. They're looking for the one sign of trouble in a sea of normalcy. But by the time they spot it, the

Cyber Supply Chain Security: A 2025 C-Suite Guide to SBOMs and C-SCRM
Learn what C-Suite leaders must know about Cyber Supply Chain Security. This guide covers SBOMs, C-SCRM, and how to protect your business from third-party risk.
Biometric Data Security: A 2025 Guide to Protecting Your Most Irreplaceable Assets
Learn essential strategies for biometric data security in 2025. Protect your most irreplaceable assets from theft, spoofing, and costly BIPA violations.
Beyond the Perimeter: Using AI to Detect Insider Threats Before They Strike
With the average cost of a single insider threat incident climbing to $15.4 million, it's clear that your greatest security risk might not be a faceless
Deepfake Vishing Attacks: The CEO Isn't Calling
Protect your company from costly deepfake vishing attacks. Our guide details how to spot AI voices, implement verification, and train your team for CEO fraud.
Deepfake-as-a-Service (DaaS) Attacks: Your 2025 Guide to Defending Against Hyper-Realistic Social Engineering
Is your business ready for Deepfake-as-a-Service? Learn to defend against AI social engineering and CEO fraud with our expert 2025 guide.
EU Cyber Resilience Act 2025: A Survival Guide for C-Suites to Ensure Compliance and Avoid Crippling Fines
The EU Cyber Resilience Act is coming in 2025. Learn what C-Suites must do to ensure compliance, manage new reporting rules, and avoid crippling fines.
SBOM Implementation Guide 2025: How to Secure Your Software Supply Chain Now
Our 2025 SBOM Implementation Guide helps CISOs & CTOs secure their software supply chain. Learn to generate and integrate SBOMs to stop attacks now.
Beyond the Firewall: A 2025 Guide to OT Security for Critical Infrastructure Protection
As a CSO, Plant Manager, or Operations Director, you're on the front lines of this new reality. The convergence of Information Technology (IT) and OT means

The Imposter in the Machine: A 2025 C-Suite Guide to Combating AI-Powered Disinformation Attacks
Protect your C-Suite from AI-Powered Disinformation. Our guide details deepfake detection, new training methods, and strategic response plans for leaders.

Post-Quantum Cryptography Readiness: A CISO's 2025 Guide to Surviving the Quantum Threat
As a security leader, you're likely feeling the pressure. The transition to new cryptographic standards feels immense, complex, and expensive. But inaction is
Countering AI-Powered Social Engineering and Deepfake Attacks with Proactive Security
Learn how to protect your organization against AI-powered social engineering and deepfake threats with next-gen strategies.
Critical SharePoint Zero‑Day CVE‑2025‑53770 Actively Exploited
A critical SharePoint zero‑day is under active attack. Learn which CVEs to patch, how to detect threats, and secure your keys.

Physical Security: Strengthening Access Control in the Digital Age
Discover how to upgrade physical security and secure your access systems against modern threats like badge cloning and tailgating.

2024 Cybersecurity Review: A Year of Unprecedented Challenges
Delve into the 2024 Cybersecurity Review for insights on the top cyber threats, trends, and defenses shaping the digital landscape this year.

Preventing Workplace Violence: Essential Strategies to Recognize, Assess, and De-escalate Threats
Preventing Workplace Violence is achievable through recognition, risk assessment, de-escalation techniques, and reporting strategies to ensure workplace safety and mitigate risks effectively.

10 Unbeatable Incident Response Planning Steps: Protect Your Business Now
Master Incident Response Planning with these 10 unbeatable steps to protect your business, minimize damage, and ensure operational continuity in the face of cyber threats.

5 Unbelievable Ways Machine Learning is Transforming Network Security
Discover 5 unbelievable ways machine learning is transforming network security and enhancing threat detection. Learn how AI improves resilience, automation, and threat prevention

Quality of Service Demystified: Top 10 Tips to Enhance Your Network
Enhance your network's Quality of Service with these top 10 actionable tips. Learn how to optimize bandwidth, prioritize critical traffic, and boost reliability.

Unlock DevSecOps Success: 7 Essential Strategies for Secure Development
Unlock DevSecOps success with 7 essential strategies for Secure Development. Enhance security, reduce risks, and build trust in your software lifecycle.

Mastering Network Function Virtualization: 10 Steps to Modernize Your Infrastructure
Master Network Function Virtualization to modernize your IT infrastructure with agility, cost efficiency, and security best practices. Learn how to implement NFV in 10 steps.

The Ultimate Guide to Cloud Security Best Practices in 2024
Discover the ultimate guide to Cloud Security Best Practices in 2024. Learn how to protect your cloud environments with encryption, access management, and compliance strategies.

Unlock Network Virtualization: 7 Incredible Benefits for Modern Networks
Discover 7 incredible benefits of Network Virtualization to improve scalability, enhance security, and reduce costs for modern network infrastructure.

5 Unbelievable Ways AI is Shaping Network Management
Discover 5 unbelievable ways AI is shaping Network Management, from predictive maintenance to real-time threat detection and automated optimization.

5 Shocking Ransomware Protection Strategies You Must Implement Now
Discover the top 5 ransomware protection strategies to safeguard your data and prevent devastating cyber attacks today.

Revolutionize Your Network Design: 5 Innovative Approaches to Scalability
Discover how to revolutionize your network design with 5 innovative approaches to scalability. Future-proof your infrastructure for enhanced performance and growth.

Unleash the Power of SIEM: 5 Incredible SIEM Benefits for Your Network Security
Unleash the power of SIEM with these 5 incredible SIEM benefits to enhance your network security and threat detection.

Avoid Access Breaches: Top 10 Identity and Access Management Best Practices
Avoid access breaches with the top 10 identity and access management best practices to secure your network.

Mastering Multi-Factor Authentication: 10 Proven Techniques to Secure Your Network
Master Multi-Factor Authentication with these 10 proven techniques to secure your network from unauthorized access.

Avoid Network Bottlenecks: Top 10 Strategies for Optimizing Network Performance
Avoid network bottlenecks with the top 10 strategies for optimizing network performance and ensuring smooth data flow.

Secure Remote Access Demystified: 7 Steps to a Bulletproof VPN
Secure remote access demystified: Follow these 7 steps to a bulletproof VPN and protect your remote connections.

Avoid Catastrophe: 7 Critical Steps to Protect Against Advanced Persistent Threats
Avoid catastrophe with these 7 critical steps to protect your network against Advanced Persistent Threats (APTs).
The Ultimate Guide to IPv6 Transition Strategies in 2024
Read the ultimate guide to IPv6 transition strategies in 2024 and prepare your network for the future.

Unlock Network Automation: 7 Powerful Techniques for Efficiency
Discover 7 powerful techniques to enhance network automation, reduce errors, and boost efficiency. Learn how SDN, APIs, and AI transform network management.

5 Ways AI in Security Operations Revolutionizes Threat Detection
Explore how AI in Security Operations boosts threat detection, automates workflows, and strengthens incident response to enhance cybersecurity defenses.

Advanced Network Security Auditing: 10 Tools You Must Know
Discover 10 advanced network security auditing tools you must know to assess and strengthen your network defenses.

10 Essential Steps to Master Software-Defined Networking (SDN): Transform Your Network
Master Software-Defined Networking with these 10 essential steps and transform your network infrastructure for the future.

Insider Threat Mitigation Strategies: 10 Proven Methods to Protect Your Organization
Insider Threat Mitigation Strategies are vital for protecting your organization. Discover 10 proven methods to prevent insider threats and safeguard sensitive data.

Mobile Device Security Practices 5 Essential Steps for Protecting Your Data
Achieve Mobile Device Security Mastery with 5 essential Mobile Device Security Practices you can’t ignore to safeguard your data.

The ROI of Cybersecurity for Small Businesses in Phoenix
The ROI of Cybersecurity. Understand how cybersecurity provides a high ROI for small businesses in Phoenix. Learn how investing in security assessments can prevent costly cyberattacks and downtime.

Uncovering Vulnerabilities: Why Your Business Needs a Physical Security Risk Assessment
Protect your business from physical security threats with a Physical Security Risk Assessment. Learn how Grab The Axe identifies vulnerabilities and ensures your facility meets safety and compliance standards to protect assets, employees, and customers.

Navigating WISP Compliance: What CPA Firms Need to Know About FTC and IRS Requirements
Ensure your CPA firm meets FTC and IRS WISP compliance requirements with expert guidance on data security. Learn how a strong Written Information Security Program protects sensitive client information and shields your firm from fines and breaches.

AI-Powered Security: The Future of Personal and Corporate Security
AI-Powered Security - Discover how AI-powered threat detection is revolutionizing security, offering faster response times and smarter, real-time monitoring for businesses and homes alike.

Grab The Axe Welcomes Andrew Luckett Jr. to Business Advisory Board
Grab The Axe (GTA) announces Andrew Luckett Jr.'s addition to its Business Advisory Board. Discover how his marketing expertise and innovative use of generative AI will enhance GTA's strategic growth in cybersecurity.

Why Phoenix Security Services Must Include Comprehensive Assessments
Discover why Phoenix security services should start with comprehensive assessments. Learn how tailored solutions can protect your business from evolving threats.

Why Resort Security Services in Phoenix Must Include Tailored Assessments
Explore how tailored resort security services in Phoenix can safeguard your property. Learn why comprehensive security assessments are vital.

Cybersecurity 2024: Why Your Business Might Be the Next Target (and How to Prevent It)
Cybersecurity 2024: Learn the top cybersecurity threats for 2024 and discover actionable steps to safeguard your business. Don’t wait until it’s too late—secure your future now.

The Importance of Healthcare Cybersecurity in Phoenix: Protecting Patient Data in a Digital Age
Healthcare Cybersecurity in Phoenix - Learn how healthcare providers in Phoenix can enhance cybersecurity measures to protect patient data and ensure compliance with regulations. Discover actionable steps and best practices for robust healthcare cybersecurity.

School Cybersecurity in Phoenix: Protecting Students and Faculty in the Digital Age
School Cybersecurity in Phoenix - Learn how schools in Phoenix can enhance cybersecurity measures to protect student and faculty data while ensuring compliance with educational regulations. Discover actionable steps and best practices for robust school cybersecurity.
10 Essential Tips for Recognizing Aggressive Body Language to Ensure Personal Safety
Learn how to recognize aggressive body language with our essential tips to ensure your personal safety. Understand key signs and stay protected.

Supporting the Arizona Horror Community
Discover how Grab The Axe supports the Arizona horror community through sponsorship of Terror Trader events like Gathering of the Ghouls and A Christmas to Dismember. Learn more about our commitment to these thrilling events and our ongoing support for horror enthusiasts.

The Future of Security: Integrating AI and GIS in Security for Comprehensive Protection
Discover how integrating AI and GIS in security can revolutionize your strategy for comprehensive protection against modern threats.

Top 10 Factors to Consider When Choosing a Security Guard Service in 2024
Discover the essential factors to consider when choosing a security guard service for businesses, residential complexes, and churches. Learn how to select the best service to meet your security needs.

Why Your Business Needs an Integrated Physical Security Approach in the Digital Age
Learn why integrated physical security is crucial for comprehensive protection in today's digital age and how to implement it in your business.

Top Cybersecurity Trends of 2024: Prepare Your Business for the Future
Discover the top cybersecurity trends for 2024 and learn how to safeguard your business against emerging threats.

Top 10 Cybersecurity Threats 2024: How to Protect Your Business
Discover the top cybersecurity threats 2024 and learn how to safeguard your business with expert tips from Grab The Axe.

Save Money and Enhance Safety with Integrated Security Solutions: Here's How!
Learn how integrated security solutions can protect your business and save you money with expert insights from Grab The Axe.

Essential Cybersecurity Communication Guide for Specialists: Effective Strategies
Learn how to effectively communicate cybersecurity strategies and risks to your supervisors and colleagues with this comprehensive cybersecurity communication guide for specialists.

Business Consulting for Small Businesses: Top 10 Key Benefits
Discover the top 10 key benefits of business consulting for small businesses. From customized strategies to enhanced innovation, learn how consulting can transform your company, increase efficiency, and drive growth. Explore expert insights and case studies in our comprehensive guide.

Business Perimeter Security Solutions: Top 5 Essential Measures
Discover the top business perimeter security solutions that can safeguard your company’s physical boundaries. This guide covers the five essential measures to protect against intrusions and ensure robust perimeter security.

Expert Strategies in Cyber Threat Mitigation: Insights from UAT’s Marcos Xochihua
Join Marcos Xochihua, a seasoned IT professional with a Master’s in Cyber Security, as he unveils his approach to cyber threat mitigation and shares his expert insights on securing digital landscapes.

Navigating Digital Security: In-depth Insights with UAT's Tristen Vaughn
Explore the vital field of digital security with Tristen Vaughn, Senior Student & Career Services Advisor at UAT. Discover strategies to protect your digital assets and stay proactive against online threats.

Robotics Cybersecurity: Protecting the Future with UAT’s NeAndrea Harris
Explore the intersection of robotics cybersecurity with NeAndrea Harris, a UAT student pioneering privacy solutions in robotics and embassy systems. Discover her journey and proactive security measures.

Mastering Security Marketing: Insights from UAT’s Stace Dixon
Discover the critical intersection of security marketing with Stace Dixon, Enrollment Marketing Manager at UAT. Learn how marketing principles enhance cybersecurity initiatives and vice versa.

Academic Cybersecurity Insights: Strategies from Professor Craig Belanger at UAT
Professor Craig Belanger shares his academic cybersecurity insights, emphasizing practical strategies for securing digital assets and combating cyber threats.

Financial Cybersecurity Strategies: Insights from Leslie Hall at UAT
Leslie Hall, Assistant Bursar at UAT, discusses financial cybersecurity strategies, emphasizing robust password management, software updates, and proactive measures to secure sensitive financial information.

Revolutionizing Community Safety: Advanced Security Solutions in Phoenix
Transforming communities with advanced security solutions in Phoenix, Arizona. Explore the innovative technologies like AI-driven surveillance and integrated cybersecurity measures enhancing protection.

Data Security Techniques: Insights from Avery Willets at UAT
Explore critical data security techniques through the experiences of Avery Willets, a University of Advanced Technology student, highlighting the intersection of data management and cybersecurity.

Personal Cybersecurity Tips: Hope Thoms on Securing the Digital Frontier at UAT
Hope Thoms, a cybersecurity student at UAT, shares valuable personal cybersecurity tips, emphasizing the use of Google’s password manager and two-factor authentication to protect digital identities.
Phoenix Security Consulting: Top 5 Essential Tips to Protect Your Business
Unlock expert Phoenix security consulting tips to safeguard your business. Grab The Axe provides strategic advice tailored to local security needs. Start protecting your enterprise today!
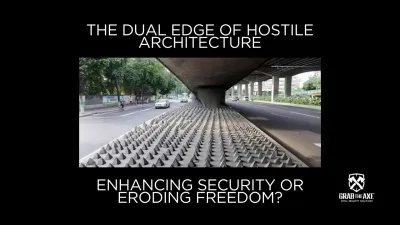
The Dual Edge of Hostile Architecture: Enhancing Security or Eroding Freedom?
Explore the intricate world of hostile architecture, a design philosophy at the crossroads of security and societal ethics. Dive into the debate, examples, and alternative approaches.

5 Shocking Secrets: Unmasking the Hidden Dangers of Aggressive Behavior
Dive into the hidden world of aggression with our eye-opening guide. Discover 5 shocking secrets behind aggressive behavior and arm yourself with strategies to navigate confrontations safely and effectively.

Cybersecurity in Computer Science Education: David Gregory's Mission for a Safer Internet
Meet David Gregory, a computer science student dedicated to enhancing internet safety. Dive into his journey of merging education with cybersecurity, offering valuable insights and advice on protecting digital spaces. Discover why cybersecurity in computer science education is crucial for navigating our digital world safely.

Gaming and Cybersecurity Insights: Navigating Digital Security in Creative Fields
Discover how Connor Elder, a game art and animation major, merges their passion for gaming with a keen awareness of cybersecurity. Learn about their proactive measures for digital and personal security, and explore insights on balancing creative pursuits with the need for robust security protocols.

Secure Game Development Insights: Daniel Diaz's Approach to Protecting Digital Creativity
Secure Game Development Insights: Meet Daniel Diaz, a game programming major, as he shares his journey into the world of secure game development. Discover how his dedication to digital arts and proactive security measures, like 2 Factor Authentication and password management, safeguard his and others' creative endeavors in the evolving landscape of game design.

Tyler's Practical Security Tips: Insights from Robotics Major Tyler Widener
Explore Tyler's Practical Security Tips from a robotics major, Tyler Widener, as he shares his unique perspective on digital security measures and future trends. Learn how to enhance your digital safety with simple yet effective strategies.

Cyber Security Education: Transforming Lives with Cyber Divisions' Outreach
Discover the transformative journey of Kibenge Francis with Cyber Divisions, and learn how you can support our mission in providing comprehensive cyber security education.

5 Revolutionary Strategies to Balance Workplace Security Psychology and Employee Well-being
Workplace Security Psychology - Discover five transformative strategies that harmonize robust security measures with the psychological well-being of employees, boosting morale and productivity without compromise.
Phoenix Arizona Security Solutions: Empowering Safety in the Valley of the Sun
Phoenix Arizona Security Solutions: Discover comprehensive security solutions in Phoenix, Arizona, with Grab The Axe. From cutting-edge technology to personalized security assessments, ensure your home or business stays protected against evolving threats. Contact us today for a tailored security strategy that meets your unique needs.

10 Essential Phoenix Neighborhood Security Tips for a Safer Community
Learn the top Phoenix Neighborhood Security Tips to keep your community safe. Discover strategies from Grab The Axe for collaborative efforts, technology integration, and personal safety education.
Revolutionizing Community Safety: Security Technology Updates in Phoenix Unveiled
Discover how Security Technology Updates in Phoenix by Grab The Axe are transforming community safety. From advanced surveillance to AI-powered solutions, embrace the future of secure, resilient neighborhoods.

Top 10 FAQs About Digital Defense: Mastering Cyber Security Risk Assessments for Businesses
Cyber Security Risk Assessments for Businesses - Elevate your business's cyber security with our comprehensive guide on Cyber Security Risk Assessments. Learn to identify, evaluate, and mitigate digital threats effectively, safeguarding your operations and reputation in the digital realm.

Essential Guide to Physical Security Assessment for Businesses: Top 10 FAQs Answered
Unlock the secrets to robust business protection with our comprehensive guide on Physical Security Assessment for Businesses, addressing the most pressing FAQs to enhance your security strategy.

5 Revolutionary Ways Integrating AI in Physical Security is a Game-Changer for Modern Businesses
Discover how integrating AI in physical security transforms modern business safety. Learn about AI's role in enhancing surveillance, predictive analysis, and ethical considerations in our comprehensive guide.

Exploring the NIST CSF 2.0 Update: 5 Critical Changes Every Cybersecurity Professional Must Know
Dive into the NIST CSF 2.0 Update to discover the five pivotal changes shaping the future of cybersecurity management and governance. Learn how the latest evolution addresses modern cyber threats and enhances organizational resilience.

What is included in a cybersecurity assessment? A Detailed Guide 2024
Discover what is included in a cybersecurity assessment with our detailed guide. From scope definition to risk analysis, learn how to secure your digital environment effectively.

Expert Home Security Consultation Services in Phoenix
Expert Home Security Consultation Services in Phoenix: Unlock the full potential of your home’s security with expert consultation services from Grab The Axe in Phoenix. Specializing in comprehensive security assessments, we provide personalized strategies to protect your home. Get in touch for bespoke security solutions designed for your peace of mind.

Business Security Services Phoenix AZ: A Strategic Approach to Safeguarding Your Enterprise
Business Security Services Phoenix AZ: Secure your Phoenix business with unparalleled security consultation services. Grab The Axe specializes in comprehensive assessments and strategic security planning tailored to your business needs in Phoenix, AZ. Protect your enterprise from threats with our expert guidance.

A UAT Student's Path in Network Security
Explore how UAT's Network Security degree shapes future cybersecurity leaders through the personal journey of a dedicated student. Dive into the world of digital defense.

Vigilant Security: Safeguarding US Business Assets Amidst the Israel-Hamas Conflict
In this comprehensive guide, we delve into the essentials of vigilant security measures for US businesses operating overseas, particularly in the context of the ongoing Israel-Hamas conflict. Discover practical strategies to protect your assets and ensure business continuity in volatile regions.

Community Support Initiatives: How Grab The Axe Contributes to Global and Local Causes
Discover Grab The Axe's dedication to global and local community support initiatives. Learn about our partnerships with organizations focused on cybersecurity education, veteran support, law enforcement, humanitarian aid, and more.

IoT Security Solutions: Navigating Challenges for a Safer Tomorrow
Explore the intricate world of IoT security solutions. Uncover the challenges, innovative solutions, and proactive strategies for a secure and interconnected future.

Secure Your Business Future with Comprehensive Physical Security Assessments
Discover the critical role of Physical Security Assessments in safeguarding your business's future. Grab The Axe specializes in comprehensive evaluations to identify and mitigate potential security threats. Learn how our tailored approach can protect your physical assets and ensure business resilience.

Data Privacy Laws Compliance: Navigating Data Privacy Laws
Data Privacy Laws Compliance: Explore essential insights into GDPR and HIPAA compliance with our comprehensive guide on navigating data privacy laws for businesses. Stay ahead in securing customer trust and maintaining legal integrity with Grab The Axe's expert solutions.

Cybersecurity Threats 2024: Stay Protected with Advanced Strategies
Explore the evolving landscape of cybersecurity threats in 2024 and learn essential strategies to protect your business from cyber attacks.

Digital Age Physical Security: Integrating Digital and Traditional Defenses
Explore the evolution of Digital Age Physical Security with Grab The Axe. Learn how integrating digital and traditional defenses can safeguard your business and home.

Traffic Safety Across Ages: Key Strategies for Safer Roads
Dive into 'Traffic Safety Across Ages' and discover groundbreaking strategies for enhancing road safety for drivers of all ages, ensuring a safer journey for everyone.
GIS Disaster Preparedness: Leveraging GIS for Disaster Preparedness Across Ages
Discover how 'GIS Disaster Preparedness' revolutionizes emergency management. From COVID-19 insights to natural disasters, explore cutting-edge strategies for safeguarding communities.

Cybersecurity GIS Mapping: Elevating Public Safety in the Digital Realm
Discover the pivotal role of 'Cybersecurity GIS Mapping' in bolstering public safety against digital threats. Learn how GIS technology is transforming the landscape of cybersecurity.
GIS Data Integration for Security: Revolutionizing Protection Strategies
Explore the transformative power of 'GIS Data Integration for Security' in revolutionizing physical security measures. Learn how this technology is pivotal in fortifying defenses against contemporary threats.

Small Business Cybersecurity Solutions: Defending Your Digital Domain
Explore vital small business cybersecurity solutions to shield your digital domain from cyber threats. Our guide covers everything from regular security assessments and employee training to robust data backup strategies and the latest in software security updates. Secure your business's future by adopting a comprehensive approach to cybersecurity, designed to fortify your operations against the evolving digital dangers. Dive into our expert insights and start defending your small business today.

GIS for Public Safety: Elevating SS4A Grant Initiatives to New Heights
Explore the pivotal role of 'GIS for Public Safety' within the SS4A Grant Program, driving innovations that safeguard communities with precision and foresight.

Essential Remote Work Security Practices in the Digital Age
Discover the ultimate guide to remote work security, covering essential practices to protect your digital workspace in the digital era. Learn how to safeguard your information against cyber threats today.

Cyber Security in Public Transport: Unveiling the Shield Against Cyber Threats in Public Transport
Explore the critical role of Cyber Security in Public Transport to thwart the silent threat of cyberattacks. Dive into our insightful analysis on safeguarding emergency responses and maintaining urban mobility.

SS4A Grants for Public Safety: Revolutionizing Public Safety
Dive deep into how SS4A Grants for Public Safety are revolutionizing urban security. Discover the transformative impact of this program on communities and how organizations like Grab The Axe are pivotal in enhancing safety measures.

External Security Consultants for Enhanced Business Protection
External Security Consultants: Unlock the strategic benefits of hiring an outside security consultant for your business. Learn how an expert's fresh perspective, specialized expertise, and tailored solutions can fortify your defenses against evolving cyber and physical threats, ensuring long-term resilience and cost efficiency.

Security Evaluations: Maximizing Financial Returns
Security Evaluations: Explore the financial advantages of integrating cybersecurity and physical security assessments into your business strategy. Uncover how these evaluations not only safeguard assets and data but also enhance operational efficiency, reduce risks, and bolster your company's reputation and trustworthiness.

Physical Security in Residential Complexes: Essential Strategies for Safeguarding Your Community
Physical Security in Residential Complexes: Discover key strategies for enhancing security in residential complexes with our comprehensive guide. Learn how to craft custom security plans, implement robust solutions, foster a secure living environment, and integrate physical and procedural measures for the utmost safety of residents.

Physical Security in Government Buildings: Comprehensive Guide to Enhancing
Physical security in government buildings, from integrating security systems to collaborating with law enforcement. Ensure your facility's safety against emerging threats with our comprehensive guide.
Strengthening Faith: Cybersecurity Practices for Religious Institutions
Explore essential Cybersecurity Practices for Religious Institutions. Learn how to protect sensitive information and maintain trust within your faith community, ensuring a secure digital environment for worship and communication.
Boost Patient Trust with Premier Security Measures for Medical Offices
Security Measures for Medical Offices - Elevate patient trust and safeguard your medical office with top-tier security measures. Contact Grab The Axe today for an unmatched security assessment and solutions tailored to your needs.

Maximizing School Campus Security: A Comprehensive Guide for Safer Educational Environments
Explore the ultimate guide to school campus security, featuring advanced strategies and technologies to ensure the safety of students, faculty, and staff. Dive into our comprehensive roadmap for creating secure educational spaces.

Property Management Security: Advanced Security Solutions
Property Management Security - Elevate tenant satisfaction and ensure asset protection with our cutting-edge security solutions for property management companies. Explore our comprehensive guide to overcoming security challenges with technology and strategic planning.

Secure the Core of Commerce: Advanced Warehouse Security Measures
Elevate your warehouse security measures with our comprehensive guide. Discover essential measures to protect your assets, ensure employee safety, and maintain operational efficiency. Secure your industrial heartbeat today.

Enhance Community Safety: Comprehensive Security Solutions for HOAs Unveiled
Comprehensive Security Solutions for HOAs - Elevate your security with our all-encompassing guide on physical and cybersecurity solutions tailored for homeowner associations. Discover how to safeguard your community and ensure peace of mind for every resident.

Fortify Your Privacy: Secure Your Home Security Cameras Today
Discover essential strategies to secure your home security cameras against hacking. Learn how to protect your privacy and enhance surveillance effectiveness with our expert tips.

Advanced Physical Security Strategies: Security Measures for Ultimate Protection
Advanced Physical Security Strategies - Unveil the secrets to bolstering physical security for safeguarding people and property. Dive into strategic measures, cutting-edge technologies, and best practices to ensure comprehensive safety in any setting.

Ultimate Guide to Security Camera Placement: Maximize Your Protection
Discover the ultimate strategies for security camera placement to enhance your property's safety. Learn from Grab The Axe experts how strategic positioning can deter intruders and ensure comprehensive surveillance.

Unlocking Tomorrow: The Bright Future of Home Security
Explore how cutting-edge advancements are shaping the future of home security. Dive into the latest trends and technologies that promise to revolutionize how we protect our homes and loved ones.
Self-Defense Firearm Selection
Embark on a journey to empower your safety with our Ultimate Guide on Self-Defense Firearm Selection. Discover essential tips, legal considerations, and expert advice to choose the right firearm for your personal protection.

Deciphering Danger: Mastering the Signs of Aggressive Body Language for Personal Safety
Unlock the secrets to recognizing the signs of aggressive body language with our expert guide. Learn how to identify potential threats and enhance your personal safety strategies today.

Empower Yourself: Mastering Essential Self-Defense Skills for Ultimate Protection
Discover the power of Essential Self-Defense Skills with our comprehensive guide. Learn how to protect yourself and your loved ones with effective, easy-to-learn techniques for ultimate personal safety.

The Ultimate Guide to Home Network Security: Revolutionize Your Safety
Discover the ultimate strategies for revolutionizing your home network security. Protect your online privacy and data against cybercrime with our expert tips and safeguard your digital life today.

Unlock Your Digital Safeguard: The Imperative for Cybersecurity Assessments
Discover the critical need for Cybersecurity Assessments to identify vulnerabilities, bolster defenses, and secure your digital future with Grab The Axe.

Small Business Security Solutions: Fortify Your Future
Discover how cutting-edge small business security solutions can safeguard your digital and physical assets against the evolving cyber threats of tomorrow. Secure the future of your business with essential strategies and technologies tailored for small businesses.

The Critical Role of Physical Security Solutions: Empowering Your Defense
Discover the critical importance of Physical Security Solutions in safeguarding people, property, and assets. Learn how Grab The Axe can fortify your defenses with a comprehensive Physical Security Assessment.

Secure Your Loved Ones: Essential Steps in Emergency Preparedness for Families
Discover essential steps in Emergency Preparedness for Families to keep your loved ones safe. Learn how a comprehensive plan, staying informed, and a tailored emergency kit can secure your family's safety.

Corporate Security Trends: Navigating the Future
Explore the latest Corporate Security Trends shaping the future, including cloud computing, IoT, and AI in security operations. Learn how Grab The Axe can help your organization stay ahead of emerging threats.
Safeguard Your Digital Life: Ultimate Cyberstalking Prevention Tips
Learn essential Cyberstalking Prevention Tips to protect your privacy online. Discover how Grab The Axe can help secure your digital life against potential cyberstalkers.
Cybersecurity Threat Landscape: Safeguard Your Future
Explore the Cybersecurity Threat Landscape with expert insights from Grab The Axe. Learn how to protect your business from viruses, phishing, and advanced cyber threats in today's digital world.
Elevate Your Protection: The Evolution of Condominium Security Solutions
Discover the future of Condominium Security Solutions with Grab The Axe. Learn how advanced surveillance, access control, and smart technology are transforming condominium security for unparalleled safety and peace of mind.

AI in Security Innovation: Revolutionize Protection
Explore the transformative role of AI in Security Innovation, uncovering its benefits and ethical considerations. Learn how Grab The Axe can guide your organization in harnessing AI for enhanced security.

Fortify Your Sanctuary: Advanced Home Security Solutions
Explore cutting-edge Home Security Solutions to protect your residence. Discover how Grab The Axe can help fortify your home against break-ins and provide unparalleled peace of mind.

Your Success: 5 Essential Data Protection Strategies for Businesses
Discover the ultimate guide to safeguarding your business with our top 5 Data Protection Strategies. Ensure your company's data and customer information are shielded against the digital threats of today's cyber landscape with Grab The Axe.

Empower Your Workforce: 5 Dynamic Employee Safety Strategies Every Business Needs
Elevate your workplace safety standards with our compelling guide on Employee Safety Strategies. Discover five essential practices to protect and empower your workforce, fostering a secure and stress-free environment for your team with Grab The Axe.

Unlock the Secrets to Unbreakable Website Security Solutions: Your Top 10 Checklist
Discover the ultimate guide to fortifying your website with our top 10 website security solutions. Protect your online presence and ensure your digital doors are locked tight against cyber threats with Grab The Axe, your trusted security partner.

Elevate Your Defense: Essential Comprehensive Physical Security Measures in Today’s Era
In an age where threats loom at every corner, understanding and implementing Comprehensive Physical Security measures has never been more crucial. Dive into our expert guide to fortify your premises and safeguard your assets with Grab The Axe's unparalleled security insights.
Guarding the Gates: Essential Cybersecurity Threats for Businesses to Overcome
Uncover the critical Cybersecurity Threats for Businesses in today's digital landscape. Protect your enterprise with our in-depth guide on combating malware, phishing, data breaches, ransomware, and cloud computing vulnerabilities with Grab The Axe.

Transform Your Security Strategy with AI-Enabled Security Solutions: A Comprehensive Case Study
Explore how AI-enabled security solutions and security systems are revolutionizing defense strategies, offering unparalleled precision and safety. Discover the future of security with our in-depth case study on AI's role in modern weaponry and protection measures.

Unleash the Power of AI Network Security: Your Ultimate Defense Against Cyber Threats
Dive into how AI network security can revolutionize your approach to safeguarding your digital assets. Explore cutting-edge strategies and ensure unparalleled protection with our expert insights.
10 Essential Active Shooting Safety Tips: How to Protect Yourself
Discover the top 10 essential active shooting safety tips to protect yourself during an active shooting. Learn proactive measures and strategies to enhance your safety and preparedness in critical situations.

Elevate Your Security Strategy with AI Drone Security Solutions: A Future-Proof Investment
Explore how AI drone security solutions are transforming site security with innovative technology, offering unparalleled surveillance, threat detection, and operational efficiency. Discover the future of safeguarding your premises today.

Unveil the Benefits of a Layered Security Strategy for Robust Protection
Discover how a Layered Security Strategy offers unparalleled protection against cyber threats. Learn the multifaceted benefits of implementing this comprehensive approach to safeguard your digital assets effectively.

Integrating Cybersecurity in Physical Security: A Crucial Strategy for Protection
Discover the critical role of cybersecurity in physical security systems. From preventing digital breaches to safeguarding sensitive data, understand why cybersecurity is not just an IT concern but a comprehensive safety strategy for protecting assets and ensuring operational continuity.

Revolutionizing Safety: How Drones in Security Are Enhancing Surveillance and Protection
Uncover the game-changing benefits of integrating drones in security strategy. Explore how drones elevate site surveillance, operational efficiency, and safety measures in our comprehensive guide.

Unlock the Power of Protection: Discover the Unmatched Benefits of a Security Assessment
Explore the transformative advantages of conducting a security assessment. Learn how it fortifies your security posture, enhances decision-making, fosters communication, offers cost savings, and provides peace of mind. Dive into our expert insights and take a decisive step towards comprehensive protection with Grab The Axe's Total Security Solutions.

Empower Your Safety: Mastering Situational Awareness Training for Ultimate Security
Uncover the indispensable benefits of situational awareness training for personal and organizational security. Learn practical strategies to enhance your alertness and preparedness in any environment, significantly reducing risks and ensuring peace of mind.
Empower Your Safety: Mastering Situational Awareness in Personal Safety
Unlock the secrets of situational awareness in personal safety. Learn how this critical skill can keep you alert, prepared, and secure in any situation. Dive into our comprehensive guide to understanding and applying situational awareness techniques for unparalleled protection in your daily life.

Dragon Security Solutions: Unlocking Mystical Security
Discover the unparalleled power of Dragon Security Solutions for safeguarding homes, businesses, and government assets. Dive into our mythical guide to unlock a new era of protection. (Easter Egg)

Self-Defense Tools: Empowering Your Safety
Unlock the power of personal safety with our guide to essential self-defense tools. Learn how to enhance your security in hand, choosing the right tools that empower you to confidently face any threat. Dive into expert advice on effective self-defense mechanisms and embrace a safer future today.

How Do I Protect My Children from Cyberbullying?
How Do I Protect My Children from Cyberbullying? Discover essential strategies to protect your children from cyberbullying. Learn how to empower them with the tools and knowledge needed to navigate online spaces safely. Our guide offers actionable steps to foster a secure digital environment for your family.

Data Breach Response: Essential Steps for Personal Protection
Data Breach Response: Learn the critical steps to take immediately after a data breach to safeguard your personal information. Our expert guide empowers you to swiftly respond and secure your identity, minimizing the impact of data breaches on your privacy.

Exploring Drone Warfare Innovations in the Ukraine Conflict: A New Era of Combat
Explore the cutting-edge Drone Warfare Innovations reshaping conflict dynamics in the Ukraine war. Discover how these technologies offer strategic advantages, from enhanced surveillance to precision strikes, and what they signify for the future of combat and security strategies.

Data Privacy Solutions: Unlock the Power of Data Privacy for Your Organization
Discover how unlocking the power of Data Privacy Solutions can transform your organization. From boosting customer trust to safeguarding against breaches, learn the steps to ensure your data is secure. Protect your reputation and unlock new growth opportunities with expert guidance.

Empower Your Defense: The Essential Guide to Martial Arts Mastery
Unlock the power of Martial Arts Mastery and safeguard your future. Dive into the essential guide that prepares you to face modern threats with confidence, offering unparalleled self-defense skills and mental fortitude. Join the ranks of those who refuse to be victims—empower your defense today.

Cyber Security Mastery: Mastering Cyber Security Today
Cyber Security Mastery - Elevate your defense against digital threats with our ultimate guide to Cyber Security Mastery. Learn how to safeguard your data and systems from sophisticated cyber-attacks and ensure the resilience of your digital frontiers.

Unveiling the Power of Drone Security Applications: A Modern Approach to Enhanced Safety
Discover the revolutionary impact of Drone Security Applications in enhancing safety protocols. From surveillance to emergency response, learn how drones are becoming indispensable in modern security strategies, offering unprecedented advantages in safeguarding assets and lives.
Penetration Testing Benefits: Maximizing Security Assurance
Penetration Testing Benefits: Discover the unparalleled benefits of penetration testing in today's digital landscape. Learn how this critical security measure can fortify your organization's defenses against sophisticated cyber threats, ensuring data integrity and compliance.

Empower and Safeguard: Prevent Sexual Assault Strategies
Prevent Sexual Assault Strategies - Unlock empowering strategies to prevent sexual assault with our comprehensive guide. Learn practical tips and self-defense techniques to enhance your safety and maintain control in any situation. Protect yourself and others by staying informed and prepared.

Drone Swarm Security Solutions: The Strategic Impact of Drone Swarms
Explore the transformative power of Drone Swarm Security Solutions in enhancing site security. From military bases to commercial properties, learn how drone swarms offer unparalleled surveillance, deterrence, and operational efficiency.

Personal Data Privacy Strategies: Guarding Your Digital Self
Dive deep into the essence of Personal Data Privacy Strategies in the digital era. Uncover the pivotal role of data privacy in safeguarding your personal information against cyber threats and learn actionable strategies to enhance your digital security today.

5 Proven Drone Defense Strategies: Shielding Against the Invisible MITM Attacks
Discover the cutting-edge Drone Defense Strategies essential for safeguarding your communications from Man-in-the-Middle (MITM) attacks. Learn how drones are transforming security protocols and how you can protect your digital landscape.

Spot Dangerous Individuals: Top 5 Essential Signs to Watch Out For
Learn how to spot dangerous individuals with our comprehensive guide. Discover the top signs to watch out for and protect yourself and your loved ones from potential threats.

The Top 5 AI Network Defense Benefits: Amazing Cybersecurity
Discover how AI Network Defense Benefits are revolutionizing cybersecurity. Learn about AI's role in enhancing network protection, scalability, customization, real-time defense, and reducing false positives.

Maximizing Safety: Unveiling Proven Effective Physical Security Strategies for Modern Threats
Explore the multi-dimensional challenges of effective physical security strategies. Uncover insights into managing risks, enhancing security postures, and the vital role of comprehensive security assessments with Grab The Axe.

Transformative Physical Security Assessment: A Case Study for Retailers
Dive into our transformative case study on how a physical security assessment can significantly bolster the security posture of large retail organizations, ensuring the safety of employees, customers, and assets.